Download Fireware Essentials Exam.Essentials.PracticeTest.2018-10-17.44q.vcex
| Vendor: | WatchGuard |
| Exam Code: | Essentials |
| Exam Name: | Fireware Essentials Exam |
| Date: | Oct 17, 2018 |
| File Size: | 504 KB |
| Downloads: | 1 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Which items are included in a Firebox backup image? (Select four.)
- Support snapshot
- Fireware OS
- Configuration file
- Log file
- Feature keys
- Certificates
Correct answer: BCEF
Explanation:
A Firebox backup image is a saved copy of the working image from the Firebox flash disk. The backup image includes the Firebox appliance software, configuration file, licenses, and certificates. When you purchase an option for your Firebox, you add a new feature key to your configuration file. Reference: Fireware Basics, Courseware: WatchGuard System Manager 10, pages 14, 57 A Firebox backup image is a saved copy of the working image from the Firebox flash disk. The backup image includes the Firebox appliance software, configuration file, licenses, and certificates.
When you purchase an option for your Firebox, you add a new feature key to your configuration file.
Reference: Fireware Basics, Courseware: WatchGuard System Manager 10, pages 14, 57
Question 2
Only 50 clients on the trusted network of your Firebox can connect to the Internet at the same time. What could cause this? (Select one.)
- TheLiveSecurity feature key is expired.
- The device feature key allows a maximum of 50 client connections.
- The DHCP address pool on the trusted interface has only 50 IP addresses.
- The Outgoing policy allows a maximum of 50 client connections.
Correct answer: C
Question 3
The IP address for the trusted interface on your Firebox is 10.0.40.1/24, but you want to change the IP address for this interface.
How can you avoid a network outage for clients on the trusted network when you change the interface IP address to 10.0.50.1/24? (Select one.)
- Create a 1-to-1 NAT rule for traffic from the 10.0.40.0/24 subnet to addresses on the 10.0.50.0/24 subnet.
- Add 10.0.40.1/24 as a secondary IP address for the interface.
- Add IP addresses on the 10.0.40.0/24 subnet to the DHCP Server IP address pool for this interface.
- Add a route to 10.0.40.0/24 with the gateway 10.0.50.1.
Correct answer: B
Question 4
Which of these options are private IPv4 addresses you can assign to a trusted interface, as described in RFC 1918, Address Allocation for Private Internets? (Select three.)
- 192.168.50.1/24
- 10.50.1.1/16
- 198.51.100.1/24
- 172.16.0.1/16
- 192.0.2.1/24
Correct answer: ABD
Question 5
The policies in a default Firebox configuration do not allow outgoing traffic from optional interfaces.
- True
- False
Correct answer: B
Question 6
When you examine the log messages In Traffic Monitor, you see that some network packets are denied with an unhandled packet log message. What does this log massage mean? (Select one.)
- The packet is denied because the site is on the Blocked Sites List.
- The packet is denied because it matched a policy.
- The packet is denied because it matched an IPS signature.
- The packet is denied because it does not match any firewall policies.
Correct answer: D
Question 7
Which of these actions adds a host to the temporary or permanent blocked sites list? (Select three.)
- Enable the AUTO-block sites that attempt to connect option in a deny policy.
- Add the site to the Blocked Sites Exceptions list.
- On the Firebox System Manager >Blocked Sites tab, select Add.
- In Policy Manager, select Setup> Default Threat Protection > Blocked Sites and click Add.
Correct answer: ACD
Explanation:
A: You can configure a deny policy to automatically block sites that originate traffic that does not comply with the policy ruleseFrom Policy Manager, double-click the PCAnywhere policy. Click the Properties tab. Select the Auto-block sites that attempt to connect checkbox. Reference: https://www.watchguard.com/training/fireware/80/defense8.htmC: The blocked sites list shows all the sites currently blocked as a result of the rules defined in Policy Manager. From this tab, you can add sites to the temporary blocked sites list, or remove temporary blocked sites.Reference: http://www.watchguard.com/training/fireware/82/monitoa6.htmD: You can use Policy Manager to permanently add sites to the Blocked Sites list.select Setup > Default Threat Protection > Blocked Sites. Click Add. The Add Site dialog box appears. Reference: http://www.watchguard.com/help/docs/wsm/xtm_11/en-US/index.html#cshid=en-US/intrusionprevention/blocked_sites_permanent_c.html A: You can configure a deny policy to automatically block sites that originate traffic that does not comply with the policy rulese
- From Policy Manager, double-click the PCAnywhere policy.
- Click the Properties tab. Select the Auto-block sites that attempt to connect checkbox.
Reference: https://www.watchguard.com/training/fireware/80/defense8.htm
C: The blocked sites list shows all the sites currently blocked as a result of the rules defined in Policy Manager. From this tab, you can add sites to the temporary blocked sites list, or remove temporary blocked sites.
Reference: http://www.watchguard.com/training/fireware/82/monitoa6.htm
D: You can use Policy Manager to permanently add sites to the Blocked Sites list.
- select Setup > Default Threat Protection > Blocked Sites.
- Click Add.
The Add Site dialog box appears.
Reference: http://www.watchguard.com/help/docs/wsm/xtm_11/en-US/index.html#cshid=en-US/intrusionprevention/blocked_sites_permanent_c.html
Question 8
Which of these threats can the Firebox prevent with the default packet handling settings? (Select four.)
- Access to inappropriate websites
- Denial of service attacks
- Flood attacks
- Malware in downloaded files
- Port scans
- Viruses in email messages
- IP spoofing
Correct answer: BCEG
Explanation:
B: The default configuration of the XTM device is to block DDoS attacks.C: In a flood attack, attackers send a very high volume of traffic to a system so it cannot examine and allow permitted network traffic. For example, an ICMP flood attack occurs when a system receives too many ICMP ping commands and must use all of its resources to send reply commands. The XTM device can protect against these types of flood attacks: IPSec, IKE, ICMP. SYN, and UDP.E: When the Block Port Space Probes (port scans) and Block Address Space Probes check boxes are selected, all incoming traffic on all interfaces is examined by the XTM device.CG: Default packet handling can reject a packet that could be a security risk, including packets that could be part of a spoofing attack or SYN flood attackReference: http://www.watchguard.com/help/docs/wsm/xtm_11/en-US/index.html#en-US/intrusionprevention/default_pkt_handling_opt_about_c.html%3FTocPath%3DDefault%2520Threat%2520Protection%7CAbout%2520Default%2520Packet%2520Handling%2520Options%7C_____0 B: The default configuration of the XTM device is to block DDoS attacks.
C: In a flood attack, attackers send a very high volume of traffic to a system so it cannot examine and allow permitted network traffic. For example, an ICMP flood attack occurs when a system receives too many ICMP ping commands and must use all of its resources to send reply commands. The XTM device can protect against these types of flood attacks: IPSec, IKE, ICMP. SYN, and UDP.
E: When the Block Port Space Probes (port scans) and Block Address Space Probes check boxes are selected, all incoming traffic on all interfaces is examined by the XTM device.
CG: Default packet handling can reject a packet that could be a security risk, including packets that could be part of a spoofing attack or SYN flood attack
Reference: http://www.watchguard.com/help/docs/wsm/xtm_11/en-US/index.html#en-US/intrusionprevention/default_pkt_handling_opt_about_c.html%3FTocPath%3DDefault%2520Threat%2520Protection%7CAbout%2520Default%2520Packet%2520Handling%2520Options%7C_____0
Question 9
How is a proxy policy different from a packet filter policy? (Select two.)
- Only a proxy policy examines information in the IP header.
- Only a proxy policy uses the IP source, destination, and port to control network traffic.
- Only a proxy policy can prevent specific threats without blocking the entire connection.
- Only a proxy works at the application, network, and transport layers to examine all connection data.
Correct answer: CD
Explanation:
C: Proxies can prevent potential threats from reaching your network without blocking the entire connection.D: A proxy operates at the application layer, as well as the network and transport layers of a TCP/IP packet, while a packet filter operates only at the network and transport protocol layers.Incorrect:Not A: A packet filter examines each packet’s IP header to control the network traffic into and out of your network.Reference: Fireware Basics, Courseware: WatchGuard System Manager 10, page 95 C: Proxies can prevent potential threats from reaching your network without blocking the entire connection.
D: A proxy operates at the application layer, as well as the network and transport layers of a TCP/IP packet, while a packet filter operates only at the network and transport protocol layers.
Incorrect:
Not A: A packet filter examines each packet’s IP header to control the network traffic into and out of your network.
Reference: Fireware Basics, Courseware: WatchGuard System Manager 10, page 95
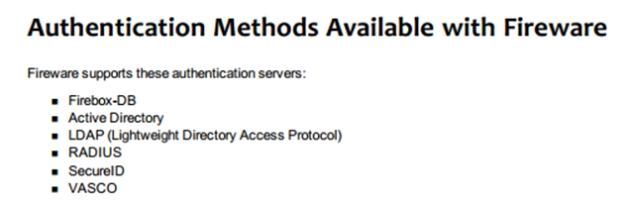
Question 10
Which authentication servers can you use with your Firebox? (Select four.)
- Active Directory
- RADIUS
- LDAP
- Linux Authentication
- Kerberos
- TACACS+
- Firebox databases
Correct answer: ABCG
Explanation:
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!




