Download Palo Alto Networks Certified Network Security Administrator.PCNSA.CertKiller.2019-04-09.15q.vcex
| Vendor: | Palo Alto Networks |
| Exam Code: | PCNSA |
| Exam Name: | Palo Alto Networks Certified Network Security Administrator |
| Date: | Apr 09, 2019 |
| File Size: | 869 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
How many zones can an interface be assigned with a Palo Alto Networks firewall?
- two
- three
- four
- one
Correct answer: D
Explanation:
Reference: https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-web-interface-help/network/network-zones/security-zone-overview Reference: https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-web-interface-help/network/network-zones/security-zone-overview
Question 2
Which two configuration settings shown are not the default? (Choose two.)
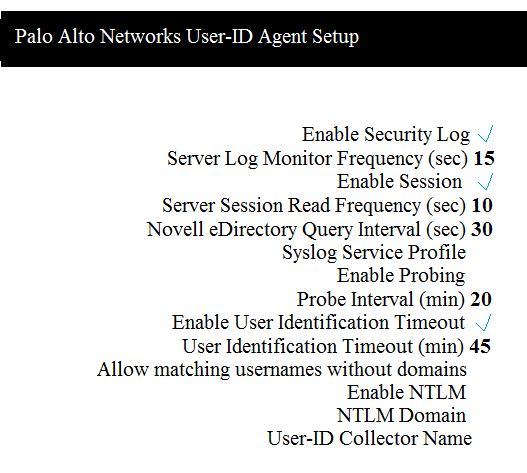
- Enable Security Log
- Server Log Monitor Frequency (sec)
- Enable Session
- Enable Probing
Correct answer: BC
Explanation:
Reference: https://docs.paloaltonetworks.com/pan-os/8-0/pan-os-web-interface-help/user-identification/device-user-identification-user-mapping/enable-server-monitoring Reference: https://docs.paloaltonetworks.com/pan-os/8-0/pan-os-web-interface-help/user-identification/device-user-identification-user-mapping/enable-server-monitoring
Question 3
Which data-plane processor layer of the graphic shown provides uniform matching for spyware and vulnerability exploits on a Palo Alto Networks Firewall?
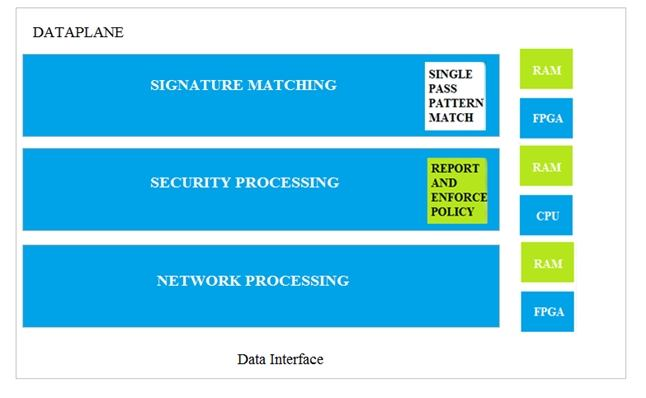
- Signature Matching
- Network Processing
- Security Processing
- Security Matching
Correct answer: A
Question 4
An administrator needs to allow users to use their own office applications. How should the administrator configure the firewall to allow multiple applications in a dynamic environment?
- Create an Application Filter and name it Office Programs, the filter it on the business-systems category, office-programs subcategory
- Create an Application Group and add business-systems to it
- Create an Application Filter and name it Office Programs, then filter it on the business-systems category
- Create an Application Group and add Office 365, Evernote, Google Docs, and Libre Office
Correct answer: B
Question 5
When creating a Source NAT policy, which entry in the Translated Packet tab will display the options Dynamic IP and Port, Dynamic, Static IP, and None?
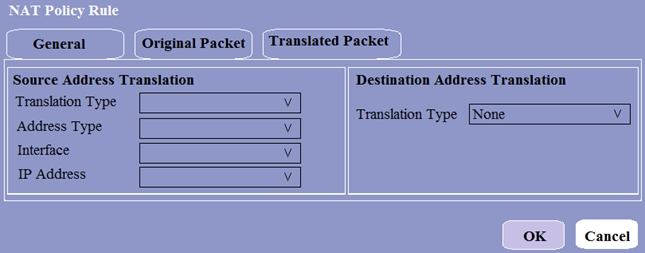
- Translation Type
- Interface
- Address Type
- IP Address
Correct answer: A
Question 6
Which interface does not require a MAC or IP address?
- Virtual Wire
- Layer3
- Layer2
- Loopback
Correct answer: A
Question 7
Which two App-ID applications will need to be allowed to use Facebook-chat? (Choose two.)
- facebook
- facebook-chat
- facebook-base
- facebook-email
Correct answer: BC
Explanation:
Reference: https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClV0CAK Reference: https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClV0CAK
Question 8
An administrator receives a global notification for a new malware that infects hosts. The infection will result in the infected host attempting to contact a command-and-control (C2) server. Which two security profile components will detect and prevent this threat after the firewall’s signature database has been updated? (Choose two.)
- vulnerability protection profile applied to outbound security policies
- anti-spyware profile applied to outbound security policies
- antivirus profile applied to outbound security policies
- URL filtering profile applied to outbound security policies
Correct answer: BD
Explanation:
Reference: https://docs.paloaltonetworks.com/pan-os/7-1/pan-os-admin/policy/create-best-practice-security-profiles Reference: https://docs.paloaltonetworks.com/pan-os/7-1/pan-os-admin/policy/create-best-practice-security-profiles
Question 9
Identify the correct order to configure the PAN-OS integrated USER-ID agent.
3. add the service account to monitor the server(s)
2. define the address of the servers to be monitored on the firewall
4. commit the configuration, and verify agent connection status
1. create a service account on the Domain Controller with sufficient permissions to execute the User- ID agent
- 2-3-4-1
- 1-4-3-2
- 3-1-2-4
- 1-3-2-4
Correct answer: D
Question 10
An administrator notices that protection is needed for traffic within the network due to malicious lateral movement activity. Based on the image shown, which traffic would the administrator need to monitor and block to mitigate the malicious activity?
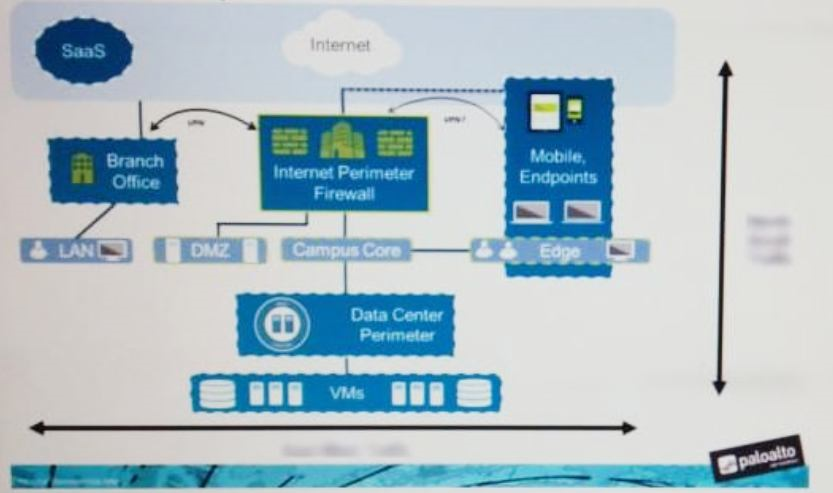
- branch office traffic
- north-south traffic
- perimeter traffic
- east-west traffic
Correct answer: D
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



