Download Information Systems Security Management Professional.CISSP-ISSMP.TestKing.2018-11-27.132q.vcex
| Vendor: | ISC |
| Exam Code: | CISSP-ISSMP |
| Exam Name: | Information Systems Security Management Professional |
| Date: | Nov 27, 2018 |
| File Size: | 110 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Which of the following is the best method to stop vulnerability attacks on a Web server?
- Using strong passwords
- Configuring a firewall
- Implementing the latest virus scanner
- Installing service packs and updates
Correct answer: D
Question 2
Which of the following is NOT a valid maturity level of the Software Capability Maturity Model (CMM)?
- Managed level
- Defined level
- Fundamental level
- Repeatable level
Correct answer: C
Question 3
Which of the following BCP teams is the first responder and deals with the immediate effects of the disaster?
- Emergency-management team
- Damage-assessment team
- Off-site storage team
- Emergency action team
Correct answer: D
Question 4
Which of the following security models dictates that subjects can only access objects through applications?
- Biba-Clark model
- Bell-LaPadula
- Clark-Wilson
- Biba model
Correct answer: C
Question 5
Which of the following types of activities can be audited for security? Each correct answer represents a complete solution. Choose three.
- Data downloading from the Internet
- File and object access
- Network logons and logoffs
- Printer access
Correct answer: BCD
Question 6
You work as a Network Administrator for ABC Inc. The company uses a secure wireless network. John complains to you that his computer is not working properly.
What type of security audit do you need to conduct to resolve the problem?
- Operational audit
- Dependent audit
- Non-operational audit
- Independent audit
Correct answer: D
Question 7
Which of the following laws is the first to implement penalties for the creator of viruses, worms, and other types of malicious code that causes harm to the computer systems?
- Gramm-Leach-Bliley Act
- Computer Fraud and Abuse Act
- Computer Security Act
- Digital Millennium Copyright Act
Correct answer: B
Question 8
Fill in the blank with an appropriate phrase.________ models address specifications, requirements, and design, verification and validation, and maintenance activities.
- Life cycle
Correct answer: 1
Question 9
You are the project manager of the GHE Project. You have identified the following risks with the characteristics as shown in the following figure:
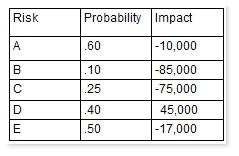
How much capital should the project set aside for the risk contingency reserve?
- $142,000
- $232,000
- $41,750
- $23,750
Correct answer: D
Explanation:
Question 10
Which of the following statements about system hardening are true? Each correct answer represents a complete solution. Choose two.
- It can be achieved by installing service packs and security updates on a regular basis.
- It is used for securing the computer hardware.
- It can be achieved by locking the computer room.
- It is used for securing an operating system.
Correct answer: AD
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



