Download Fortinet Network Security Expert 8 Written Exam (NSE8 810 - FortiOS 5.6).NSE8_810.PremDumps.2019-04-20.39q.vcex
| Vendor: | Fortinet |
| Exam Code: | NSE8_810 |
| Exam Name: | Fortinet Network Security Expert 8 Written Exam (NSE8 810 - FortiOS 5.6) |
| Date: | Apr 20, 2019 |
| File Size: | 2 MB |
| Downloads: | 1 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
You want to manage a FortiGate with the FortiCloud service.
The FortiGate shows up in your list of devices on the FortiGate Web Site, but all management functions are either missing or grayed out. Which statement is correct in this scenario?
- The managed FortiGate is running a version of FortiOS that is either too new or too old for FortiCloud.
- The managed FortiGate requires that a FortiCloud management license be purchased and applied.
- You must manually configure system central-management on the FortiGate CLI and set the management type to fortiguard.
- The management tunnel mode on the managed FortiGate must be changed to normal.
Correct answer: C
Question 2
FortiMail is configured with the protected domain “internal.lab”.
Which two envelope addresses will need an access control rule to relay e-mail sent for unauthenticated users? (Choose two.)
- MAIL FROM: [email protected];RCPT TO;[email protected]
- MAIL FROM: [email protected];RCPT TO;[email protected]
- MAIL FROM: [email protected];RCPT TO;[email protected]
- MAIL FROM: student@ internal.lab;RCPT TO;[email protected]
Correct answer: BC
Question 3
You deploy a FortiGate device in a remote office based on the requirements shown below.
- Due to company’s security policy, management IP of your FortiGate is not allowed to access the Internet.
- Apply Web Filtering, AntiVirus, IPS and Application control to the protected subnet.
- Be managed by a central FortiManager on the head office.
Which action will help to achieve the requirements?
- Configure a default route and make sure that the FortiGate device can ping to service.fortiguard.net
- Configure the FortiGuard override server and use the IP address of the FortiManager.
- Configure the FortiGuard override server and use the IP address of service.fortiguard.net.
- Configure FortiGuard to use FortiGuard Filtering Port 8888.
Correct answer: B
Question 4
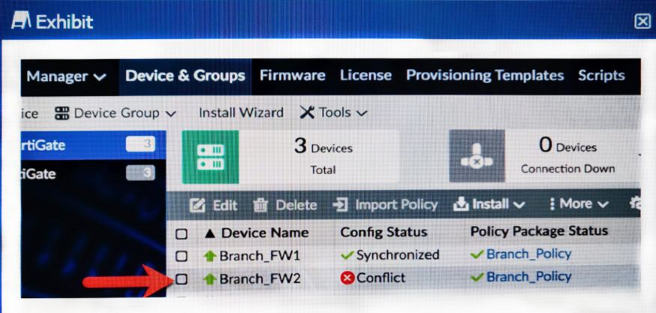
You log into FortiManager, look at the Device Manager window and notice that one of your managed devices is not in normal status.
Referring to the exhibit, which two statements correctly describe the affected device’s status and result? (Choose two.)
- The device configuration was changed on the local FortiGate side only; auto-update is disabled.
- The device configuration was changed on both the local FortiGate side and the FortiManager side; auto-update is disabled.
- The changed configuration on the FortiGate will remain the next time that the device configuration is pushed form FortiManager.
- The changed configuration on the FortiGate will be overwritten in favor of what is on the FortiManager the next time that the device configuration is pushed.
Correct answer: BD
Question 5
A FortiOS device is used for termination of VPNs for a number of remote spoke VPN units (designated Group A spokes) using a phase 1 main mode dial-up tunnel using pre-shared keys. Your company recently acquired another organization. You are asked to establish VPN connectivity for the newly acquired organization’s sites for which new devices will be provisioned (designated Group B spokes). Both existing (Group A) and new (Group B) spoke units are dynamically addressed. You are asked to ensure that spokes from the acquired organization (Group B) have different access permissions that your existing VPN spokes units (Group A).
Which two solutions meet the requirements for the new spoke group? (Choose two.)
- Implement a new phase 1 dial-up main mode tunnel with preshared keys and XAuth. Use identity policies to filter traffic.
- Implement a new phase 1 dial-up main mode tunnel with a different pre-shared key than Group A spokes. Use standard policies to filter traffic for the new dial-up tunnel.
- Implement a new phase 1 dial-up main mode tunnel with certificate authentication. Use standard policies to filter traffic for the new dial-up tunnel.
- Implement separate phase 1 dial-up aggressive mode tunnels with a distinct peer ID. Use standard policies to filter traffic for the new dial-up tunnel.
Correct answer: AB
Question 6
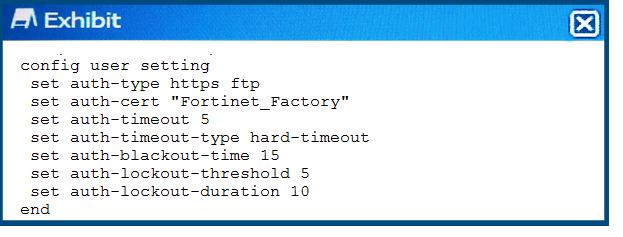
Referring to the exhibit, which two statements are true about local authentication? (Choose two.)
- The user will be blocked 15 seconds after five login failures.
- When a ClientHello message indicating a renegotiation is received, the FortiGate will allow the TCP connection.
- The user’s IP address will be blocked 15 seconds after five login failures.
- After five minutes, the user will need to re-authenticate.
Correct answer: CD
Question 7
You created an aggregate interface between your FortiGate and a switch consisting of two 1 Gbps links as shown in the exhibit. However, the maximum bandwidth never exceeds. 1 Gbps and employees are complaining that the network is slow. After troubleshooting, you notice only one member interface is being used. The configuration for the aggregate interface is shown in the exhibit.
In this scenario, which command will solve this problem?
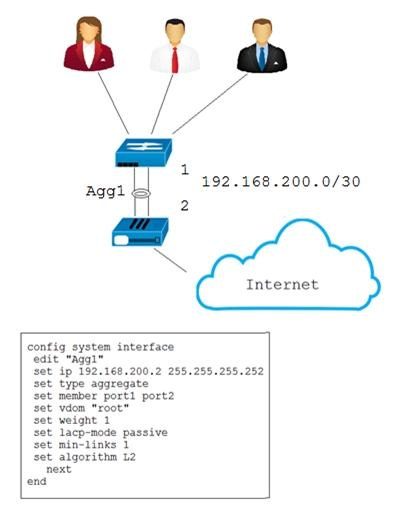
- config system interfaceedit Agg1set min-links 2end
- config system interfaceedit Agg1set weight 2end
- config system interfaceedit Agg1set Algorithm L4end
- config system interfaceedit Agg1set lacp-mode activeend
Correct answer: A
Question 8
You are trying to configure Link-Aggregation Group (LAG), but ports A and B do not appear on the list of member options. Referring to the exhibit, which statement is correct in this situation?
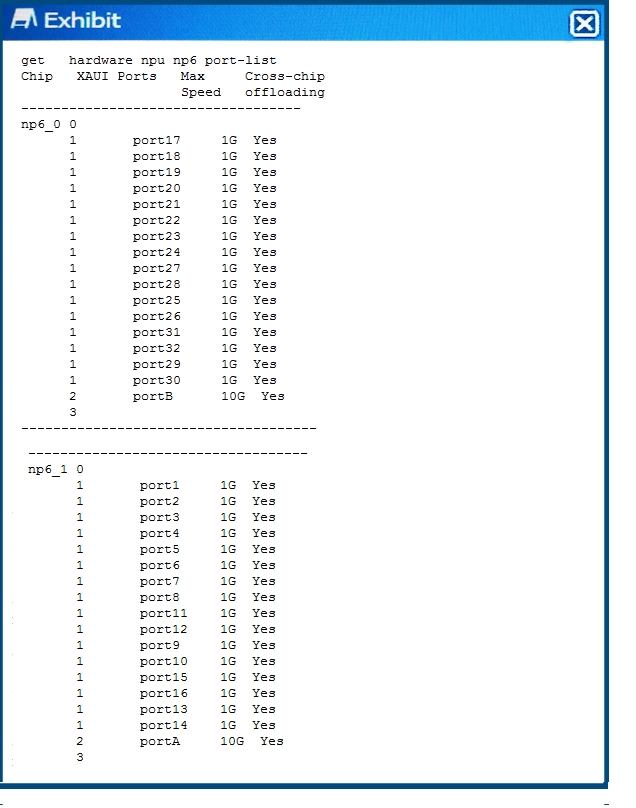
- The FortiGate model being used does not support LAG.
- The FortiGate model does not have an Integrated Switch Fabric (ISF).
- The FortiGate SFP+ slot does not have the correct module.
- The FortiGate interfaces are defective and require replacement.
Correct answer: B
Question 9
You need to apply the security features below to the network shown in the exhibit.
- high grade DDoS protection
- Web security and load balancing for Server1 and Server2
- Solution must be PCI DSS compliant
- Enhanced security to DNS 1 and DNS 2
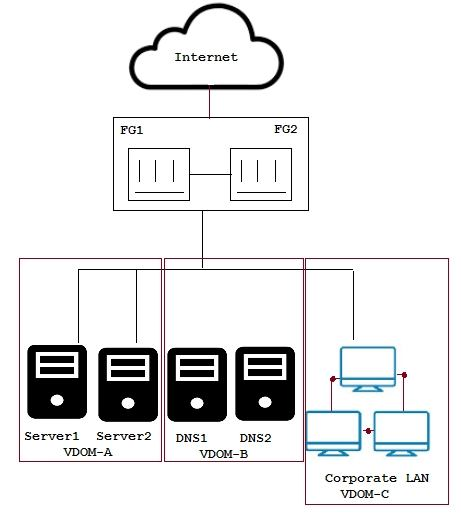
What are three solutions for this scenario? (Choose three.)
- FortiWeb for VDOM-A
- FortiDDoS between FG1 and FG2 and the Internet
- FortiADC for VDOM-A
- FortiADC for VDOM-B
- FortiDDoS between FG1 and FG2 and VDOMs
Correct answer: CDE
Question 10
An Administrator reports continuous high CPU utilization on a FortiGate device due to the IPS engine. The exhibit shows the global IPS configuration. Which two configuration actions will reduce the CPU usage? (Choose two.)
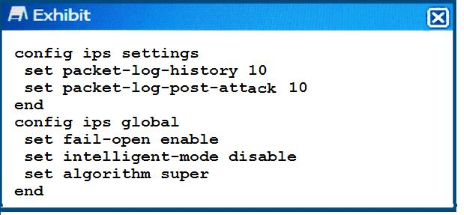
- Disable fail open
- Enable intelligent mode
- Change the algorithm to low
- Reduce the number of packets being logged
Correct answer: CD
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



