Download Fortinet NSE 6 -FortiMail 7-2.NSE6_FML-7.2.VCEplus.2023-08-21.17q.vcex
| Vendor: | Fortinet |
| Exam Code: | NSE6_FML-7.2 |
| Exam Name: | Fortinet NSE 6 -FortiMail 7-2 |
| Date: | Aug 21, 2023 |
| File Size: | 2 MB |
| Downloads: | 2 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Refer to the exhibits which show a topology diagram (Topology), and a configuration element (Access Control Rule).
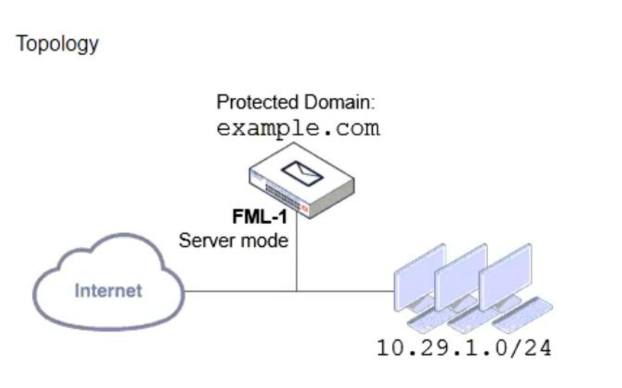
An administrator must enforce authentication on FML-1 for all outbound email from the example.com domain.
Which two settings should be used to configure the access receive rule? (Choose two.)
- The Sender IP/netmask should be set to 10.29.1.0/24.
- The Action should be set to Reject
- The Recipient pattern should be set to * @example. com.
- The Authentication status should be set to Authenticated
Correct answer: AD
Question 2
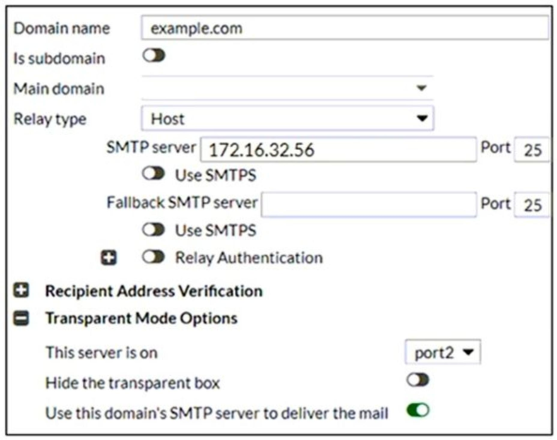
Refer to the exhibit which displays a topology diagram.

Which two statements describe the built-in bridge functionality on a transparent mode FortiMail? (Choose two.)
- If port1. is required to process SMTP traffic, it must be configured as a routed interface.
- All bridge member interfaces belong to the same subnet as the management IP.
- The management IP is permanently tied to port1, and port1 cannot be removed from the bridge.
- Any bridge member interface can be removed from the bridge and configured as a routed interface.
Correct answer: BC
Question 3
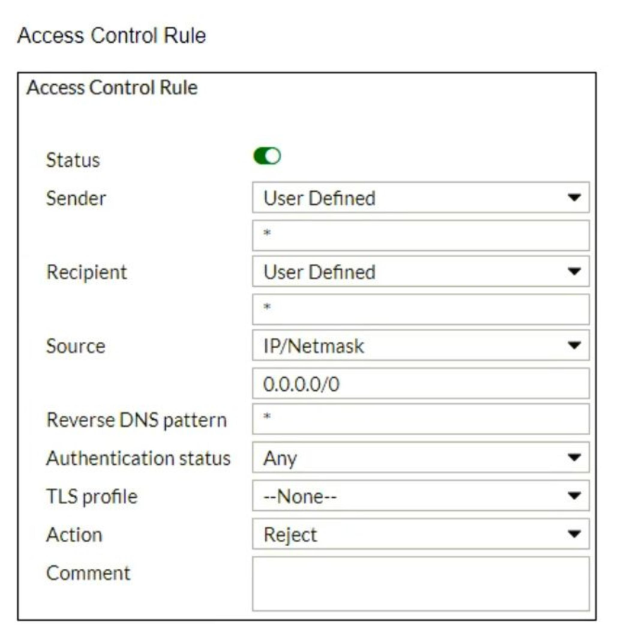
Refer to the exhibit which displays the domain configuration of a transparent mode FortiMail device.
Based on the exhibit, which two sessions are considered incoming sessions? (Choose two.)
- DESTINATION IP: 172.16.32.56 MAIL FROM: [email protected] RCPT TO: [email protected]
- DESTINATION IP: 192.168.54.10 MAIL FROM: [email protected] RCPT TO: [email protected]
- DESTINATION IP: 10.25.32.15 MAIL FROM: [email protected] RCPT TO: [email protected]
- DESTINATION IP: 172.16.32.56 MAIL FROM: [email protected] RCPT TO: [email protected]
Correct answer: AD
Question 4
Refer to the exhibit, which shows an inbound recipient policy.

After creating the policy shown in the exhibit, an administrator discovers that clients can send unauthenticated emails using SMTP.
What must the administrator do to enforce authentication?
- Move this incoming recipient policy to the top of the list.
- Configure a matching IP policy with the exclusive flag enabled.
- Configure an access delivery rule to enforce authentication.
- Configure an access receive rule to verily authentication status.
Correct answer: D
Question 5
Refer to the exhibits, which display a topology diagram (Topology) and two FortiMail device configurations (FML1 Configuration and FML2 Configuration).
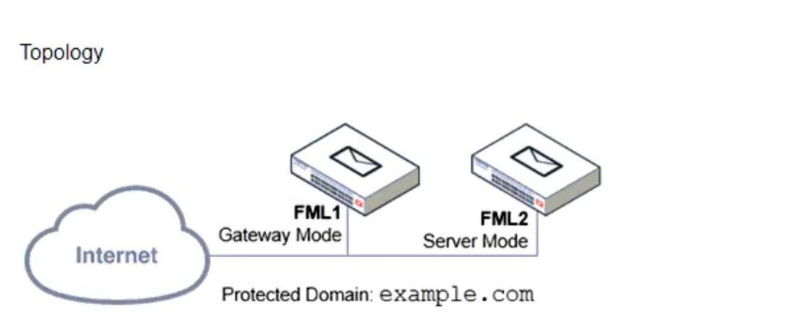
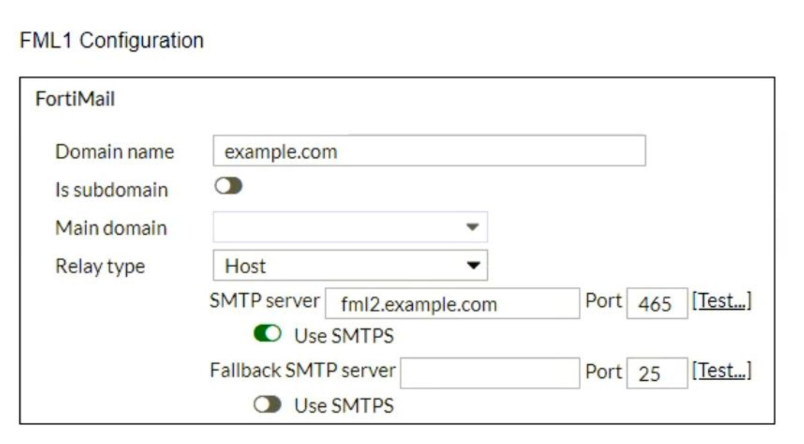
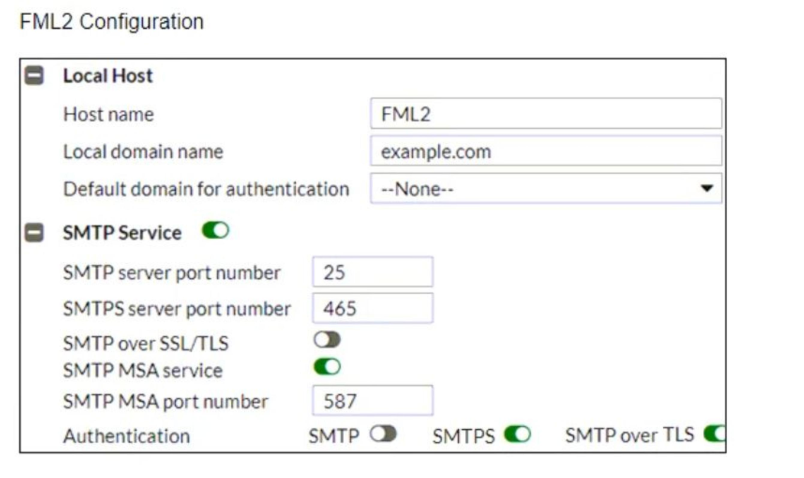
What is the expected outcome of SMTP sessions sourced from FML1 and destined for FML2?
- FML1 will fail to establish any connection with FML2.
- FML1 will attempt to establish an SMTPS session with FML2. but fail and revert to standard SMTP.
- FML1 will send the STARTTLS command in the SMTP session, which will be rejected by FML2.
- FML1 will successfully establish an SMTPS session with FML2.
Correct answer: D
Question 6
Refer to the exhibit which displays a history log entry.

Why does the last field show SYSTEM in the Policy ID column?
- The email was dropped by a system blocklist.
- It is an inbound email.
- The email matched a system-level authentication policy.
- The email did not match a recipient-based policy.
Correct answer: D
Question 7
Which two FortiMail antispam techniques can you use to combat zero-day spam? (Choose two.)
- IP reputation
- Spam outbreak protection
- DNSBL
- Behavior analysis
Correct answer: AB
Question 8
Refer to the exhibit which shows an nslookup output of MX records of the example.com domain.

Which two MTA selection behaviors for the example.com domain are correct? (Choose two.)
- mx.example.com will receive approximately twice the number of email as mx.hosted.com because of its preference value.
- The primary MTA for the example.com domain is mx.hosted.com.
- The external MTAs will send email to mx.example.com only if mx.hosted.com is unreachable.
- The PriNS server should receive all email for the example.com domain.
Correct answer: BC
Question 9
While reviewing logs, an administrator discovers that an incoming email was processed using policy IDs 0:4:9:INTERNAL.
Which two statements describe what this policy ID means? (Choose two.)
- Access control policy number 9 was used.
- The FortiMail configuration is missing an access delivery rule.
- The email was processed using IP-based policy ID 4.
- FortiMail is applying the default behavior for relaying inbound email.
Correct answer: AC
Question 10
Refer to the exhibit which shows a topology diagram of a FortiMail cluster deployment.
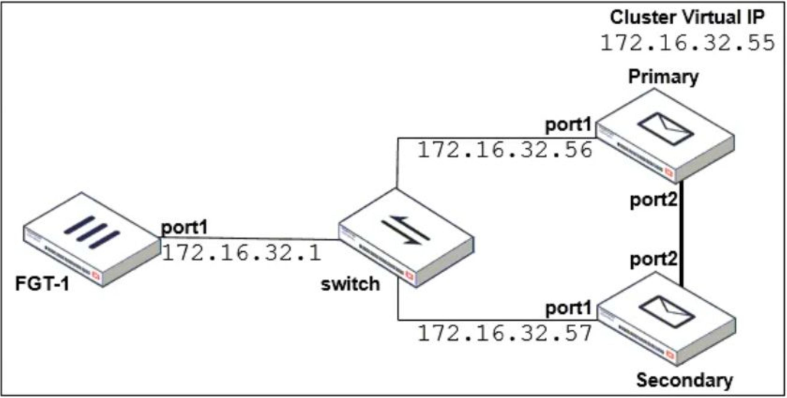
Which IP address must the DNS MX record for this organization resolve to?
- 1172 16 32 57
- 172.16.32.56
- 172.16.32.55
- 172.16.32.1
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



