Download Fortinet NSE 5 - FortiManager 7.0.NSE5_FMG-7.0.NewDumps.2023-08-04.32q.vcex
| Vendor: | Fortinet |
| Exam Code: | NSE5_FMG-7.0 |
| Exam Name: | Fortinet NSE 5 - FortiManager 7.0 |
| Date: | Aug 04, 2023 |
| File Size: | 1 MB |
| Downloads: | 8 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Which three settings are the factory default settings on FortiManager? (Choose three.)
- Username is admin
- Password is fortinet
- FortiAnalyzer features are disabled
- Reports and Event Monitor panes are enabled
- port1 interface IP address is 192.168.1.99/24
Correct answer: ACE
Question 2
View the following exhibit.
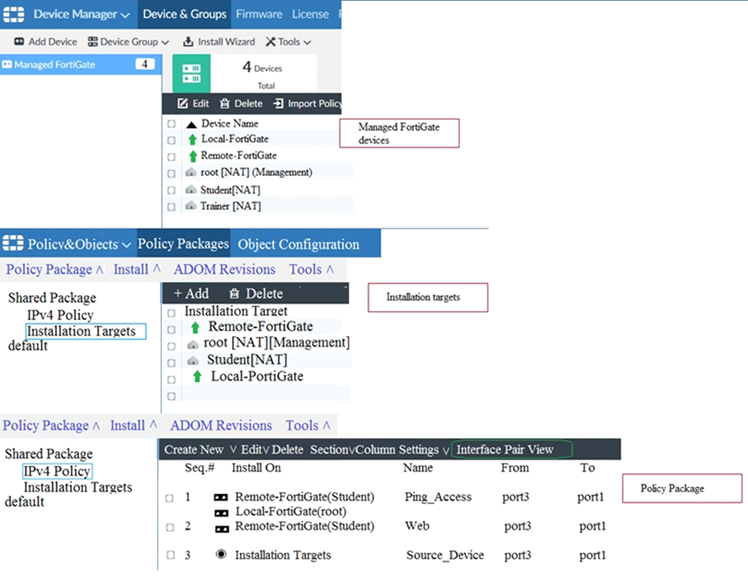
Given the configurations shown in the exhibit, what can you conclude from the installation targets in the Install On column?
- The Install On column value represents successful installation on the managed devices
- Policy seq#3 will be installed on all managed devices and VDOMs that are listed under Installation Targets
- Policy seq#3 will be installed on the Trainer[NAT] VDOM only
- Policy seq#3 will be not installed on any managed device
Correct answer: B
Question 3
View the following exhibit:
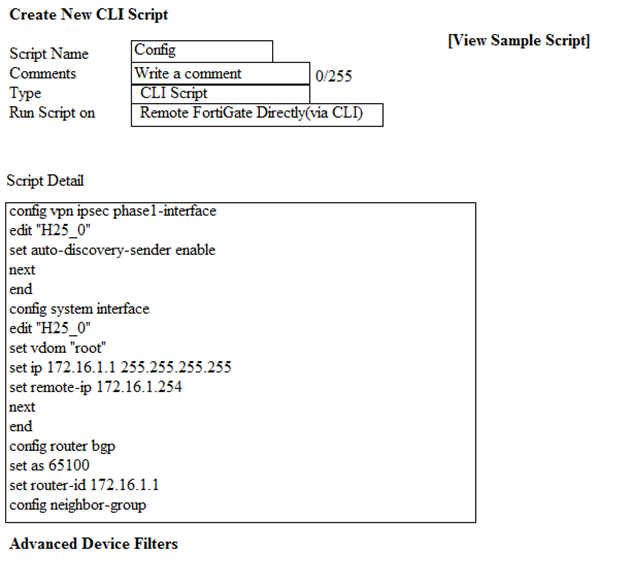
Which two statements are true if the script is executed using the Remote FortiGate Directly (via CLI) option? (Choose two.)
- You must install these changes using Install Wizard
- FortiGate will auto-update the FortiManager’s device-level database.
- FortiManager will create a new revision history.
- FortiManager provides a preview of CLI commands before executing this script on a managedFortiGate.
Correct answer: BC
Question 4
An administrator with the Super_User profile is unable to log in to FortiManager because of an authentication failure message. Which troubleshooting step should you take to resolve the issue?
- Make sure FortiManager Access is enabled in the administrator profile
- Make sure Offline Mode is disabled
- Make sure the administrator IP address is part of the trusted hosts.
- Make sure ADOMs are enabled and the administrator has access to the Global ADOM
Correct answer: C
Explanation:
Even if a user entered the correct userid/password, the FMG denies access if a user is logging in from an untrusted source IP subnets. Reference: https://docs.fortinet.com/document/fortimanager/6.0.3/administration-guide/107347/trusted-hosts Even if a user entered the correct userid/password, the FMG denies access if a user is logging in from an untrusted source IP subnets.
Reference: https://docs.fortinet.com/document/fortimanager/6.0.3/administration-guide/107347/trusted-hosts
Question 5
View the following exhibit.
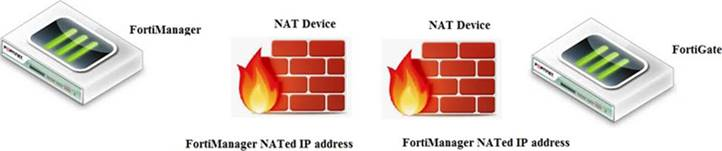
If both FortiManager and FortiGate are behind the NAT devices, what are the two expected results? (Choose two.)
- FortiGate is discovered by FortiManager through the FortiGate NATed IP address.
- FortiGate can announce itself to FortiManager only if the FortiManager IP address is configured on FortiGate under central management.
- During discovery, the FortiManager NATed IP address is not set by default on FortiGate.
- If the FCFM tunnel is torn down, FortiManager will try to re-establish the FGFM tunnel.
Correct answer: AC
Explanation:
Fortimanager can discover FortiGate through a NATed FortiGate IP address. If a FortiManager NATed IP address is configured on FortiGate, then FortiGate can announce itself to FortiManager. FortiManager will not attempt to re-establish the FGFM tunnel to the FortiGate NATed IP address, if the FGFM tunnel is interrupted. Just like it was in the NATed FortiManager scenario, the FortiManager NATed IP address in this scenario is not configured under FortiGate central management configuration. Fortimanager can discover FortiGate through a NATed FortiGate IP address. If a FortiManager NATed IP address is configured on FortiGate, then FortiGate can announce itself to FortiManager. FortiManager will not attempt to re-establish the FGFM tunnel to the FortiGate NATed IP address, if the FGFM tunnel is interrupted. Just like it was in the NATed FortiManager scenario, the FortiManager NATed IP address in this scenario is not configured under FortiGate central management configuration.
Question 6
Refer to the exhibit.
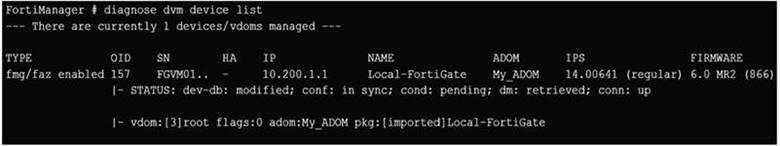
Which two statements about the output are true? (Choose two.)
- The latest revision history for the managed FortiGate does match with the FortiGate running configuration
- Configuration changes have been installed to FortiGate and represents FortiGate configuration has been changed
- The latest history for the managed FortiGate does not match with the device-level database
- Configuration changes directly made on the FortiGate have been automatically updated to device-leveldatabase
Correct answer: AC
Explanation:
STATUS: dev-db: modified; conf: in sync; cond: pending; dm: retrieved; conn: up– dev-db: modified –This is the device setting status which indicates that configuration changes were made on FortiManager. – conf: in sync – This is the sync status which shows that the latest revision history is in sync with Fortigate’s configuration.– cond: pending – This is the configuration status which says that configuration changes need to be installed. Most probably a retrieve was done in the past (dm: retrieved) updating the revision history DB (conf: in sync) and FortiManager device level DB, now there is a new modification on FortiManager device level DB (dev-db: modified) which wasn’t installed to FortiGate (cond: pending), hence; revision history DB is not aware of that modification and doesn’t match device DB. Conclusion:– Revision DB does match FortiGate.– No changes were installed to FortiGate yet.– Device DB doesn’t match Revision DB.– No changes were done on FortiGate (auto-update) but configuration was retrieved instead After an Auto-Update or Retrieve:device database = latest revision = FGTThen after a manual change on FMG end (but no install yet):latest revision = FGT (still) but now device database has been modified (is different).After reverting to a previous revision in revision history:device database = reverted revision != FGT STATUS: dev-db: modified; conf: in sync; cond: pending; dm: retrieved; conn: up– dev-db: modified –
This is the device setting status which indicates that configuration changes were made on FortiManager.
– conf: in sync – This is the sync status which shows that the latest revision history is in sync with Fortigate’s configuration.– cond: pending – This is the configuration status which says that configuration changes need to be installed.
Most probably a retrieve was done in the past (dm: retrieved) updating the revision history DB (conf: in sync) and FortiManager device level DB, now there is a new modification on FortiManager device level DB (dev-db: modified) which wasn’t installed to FortiGate (cond: pending), hence; revision history DB is not aware of that modification and doesn’t match device DB.
Conclusion:– Revision DB does match FortiGate.– No changes were installed to FortiGate yet.– Device DB doesn’t match Revision DB.– No changes were done on FortiGate (auto-update) but configuration was retrieved instead
After an Auto-Update or Retrieve:device database = latest revision = FGT
Then after a manual change on FMG end (but no install yet):latest revision = FGT (still) but now device database has been modified (is different).
After reverting to a previous revision in revision history:device database = reverted revision != FGT
Question 7
View the following exhibit, which shows the Download Import Report:
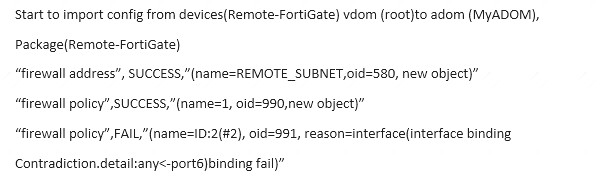
Why it is failing to import firewall policy ID 2?
- The address object used in policy ID 2 already exist in ADON database with any as interface association and conflicts with address object interface association locally on the FortiGate
- Policy ID 2 is configured from interface any to port6 FortiManager rejects to import this policy because any interface does not exist on FortiManager
- Policy ID 2 does not have ADOM Interface mapping configured on FortiManager
- Policy ID 2 for this managed FortiGate already exists on FortiManager in policy package named Remote-FortiGate.
Correct answer: A
Explanation:
FortiManager_6.4_Study_Guide-Online – page 331 & 332 FortiManager_6.4_Study_Guide-Online – page 331 & 332
Question 8
View the following exhibit.
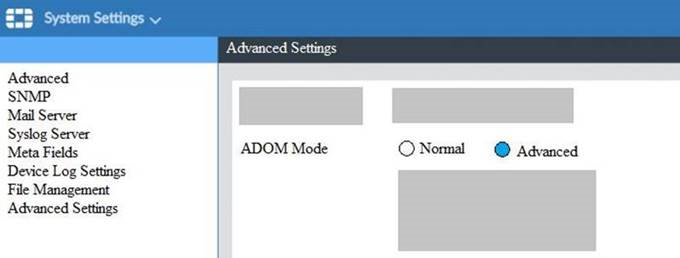
What is the purpose of setting ADOM Mode to Advanced?
- The setting allows automatic updates to the policy package configuration for a managed device
- The setting enables the ADOMs feature on FortiManager
- This setting allows you to assign different VDOMs from the same FortiGate to different ADOMs.
- The setting disables concurrent ADOM access and adds ADOM locking
Correct answer: C
Explanation:
Reference:https://docs.fortinet.com/document/fortianalyzer/7.0.0/administration-guide/66530/adom-device-modes Reference:
https://docs.fortinet.com/document/fortianalyzer/7.0.0/administration-guide/66530/adom-device-modes
Question 9
An administrator run the reload failure command: diagnose test deploymanager reload config <deviceid> on FortiManager. What does this command do?
- It downloads the latest configuration from the specified FortiGate and performs a reload operation on the device database.
- It installs the latest configuration on the specified FortiGate and update the revision history database.
- It compares and provides differences in configuration on FortiManager with the current running configuration of the specified FortiGate.
- It installs the provisioning template configuration on the specified FortiGate.
Correct answer: A
Explanation:
Reference:https://community.fortinet.com/t5/FortiManager/Technical-Note-Retrieve-configuration-file-using-CLI-from-a/t Reference:
https://community.fortinet.com/t5/FortiManager/Technical-Note-Retrieve-configuration-file-using-CLI-from-a/t
Question 10
View the following exhibit.
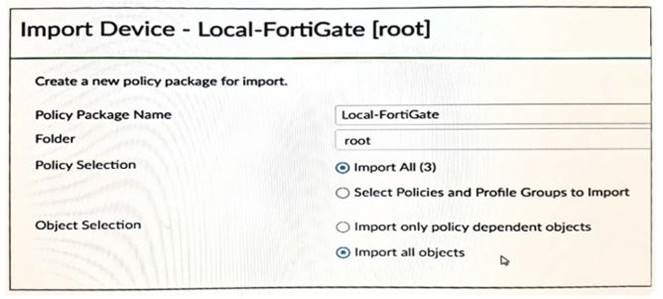
An administrator is importing a new device to FortiManager and has selected the shown options. What will happen if the administrator makes the changes and installs the modified policy package on this managed FortiGate?
- The unused objects that are not tied to the firewall policies will be installed on FortiGate
- The unused objects that are not tied to the firewall policies will remain as read-only locally on FortiGate
- The unused objects that are not tied to the firewall policies locally on FortiGate will be deleted
- The unused objects that are not tied to the firewall policies in policy package will be deleted from the FortiManager database
Correct answer: C
Explanation:
Reference:https://community.fortinet.com/t5/FortiManager/Import-all-objects-Versus-Import-only-policy-dependent-objec Reference:
https://community.fortinet.com/t5/FortiManager/Import-all-objects-Versus-Import-only-policy-dependent-objec
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



