Download Fortinet NSE 4 -FortiOS 7-2.NSE4_FGT-7.2.PremiumDumps.2024-02-26.164q.vcex
| Vendor: | Fortinet |
| Exam Code: | NSE4_FGT-7.2 |
| Exam Name: | Fortinet NSE 4 -FortiOS 7-2 |
| Date: | Feb 26, 2024 |
| File Size: | 11 MB |
| Downloads: | 1 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Which two statements are correct about NGFW Policy-based mode? (Choose two.)
- NGFW policy-based mode does not require the use of central source NAT policy
- NGFW policy-based mode can only be applied globally and not on individual VDOMs
- NGFW policy-based mode supports creating applications and web filtering categories directly in a firewall policy
- NGFW policy-based mode policies support only flow inspection
Correct answer: CD
Question 2
Refer to the exhibit.
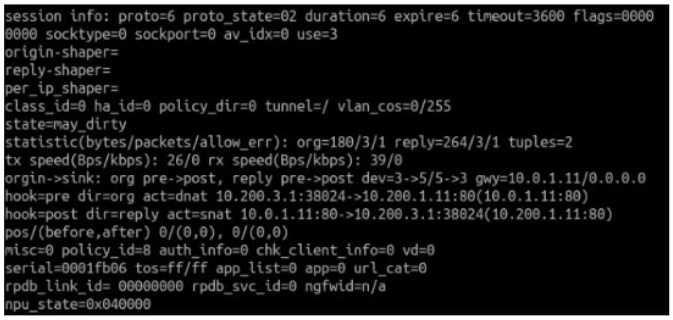
Which contains a session diagnostic output. Which statement is true about the session diagnostic output?
- The session is in SYN_SENT state.
- The session is in FIN_ACK state.
- The session is in FTN_WAIT state.
- The session is in ESTABLISHED state.
Correct answer: A
Explanation:
Indicates TCP (proto=6) session in SYN_SENT state (proto_state=2) Reference: https://kb.fortinet.com/kb/viewContent.do?externalId=FD30042 Indicates TCP (proto=6)
session in SYN_SENT state (proto_state=2)
Reference:
https://kb.fortinet.com/kb/viewContent.do?externalId=FD30042
Question 3
Which two statements explain antivirus scanning modes? (Choose two.)
- In proxy-based inspection mode, files bigger than the buffer size are scanned.
- In flow-based inspection mode, FortiGate buffers the file, but also simultaneously transmits it to the client.
- In proxy-based inspection mode, antivirus scanning buffers the whole file for scanning, before sending it to the client.
- In flow-based inspection mode, files bigger than the buffer size are scanned.
Correct answer: BC
Explanation:
An antivirus profile in full scan mode buffers up to your specified file size limit. The default is 10 MB. That is large enough for most files, except video files. If your FortiGate model has more RAM, you may be able to increase this threshold. Without a limit, very large files could exhaust the scan memory. So, this threshold balances risk and performance. Is this tradeoff unique to FortiGate, or to a specific model? No. Regardless of vendor or model, you must make a choice. This is because of the difference between scans in theory, that have no limits, and scans on real-world devices, that have finite RAM. In order to detect 100% of malware regardless of file size, a firewall would need infinitely large RAM--something that no device has in the real world. Most viruses are very small. This table shows a typical tradeoff. You can see that with the default 10 MB threshold, only 0.01% of viruses pass through. An antivirus profile in full scan mode buffers up to your specified file size limit. The default is 10 MB. That is large enough for most files, except video files. If your FortiGate model has more RAM, you may be able to increase this threshold. Without a limit, very large files could exhaust the scan memory. So, this threshold balances risk and performance. Is this tradeoff unique to FortiGate, or to a specific model? No. Regardless of vendor or model, you must make a choice. This is because of the difference between scans in theory, that have no limits, and scans on real-world devices, that have finite RAM. In order to detect 100% of malware regardless of file size, a firewall would need infinitely large RAM--something that no device has in the real world. Most viruses are very small. This table shows a typical tradeoff. You can see that with the default 10 MB threshold, only 0.01% of viruses pass through.
Question 4
Refer to the web filter raw logs.
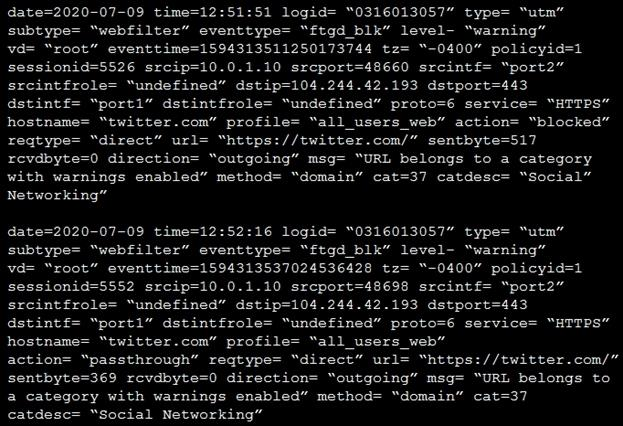
Based on the raw logs shown in the exhibit, which statement is correct?
- Social networking web filter category is configured with the action set to authenticate.
- The action on firewall policy ID 1 is set to warning.
- Access to the social networking web filter category was explicitly blocked to all users.
- The name of the firewall policy is all_users_web.
Correct answer: A
Explanation:
We have two logs, first with action deny and second with passthrough. Remember ... action="passthrough" mean that authentication has occurred We have two logs, first with action deny and second with passthrough.
Remember ... action="passthrough" mean that authentication has occurred
Question 5
Which two configuration settings are synchronized when FortiGate devices are in an active-active HA cluster?
(Choose two.)
- FortiGuard web filter cache
- FortiGate hostname
- NTP
- DNS
Correct answer: CD
Question 6
An administrator wants to configure timeouts for users. Regardless of the user’s behavior, the timer should start as soon as the user authenticates and expire after the configured value.
Which timeout option should be configured on FortiGate?
- auth-on-demand
- soft-timeout
- idle-timeout
- new-session
- hard-timeout
Correct answer: E
Explanation:
Security Guide P167 Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD37221 Security Guide P167
Reference:
https://kb.fortinet.com/kb/documentLink.do?externalID=FD37221
Question 7
Why does FortiGate Keep TCP sessions in the session table for several seconds, even after both sides (client and server) have terminated the session?
- To allow for out-of-order packets that could arrive after the FIN/ACK packets
- To finish any inspection operations
- To remove the NAT operation
- To generate logs.
Correct answer: A
Explanation:
TCP provides the ability for one end of a connection to terminate its output while still receiving data from the other end. This is called a half-close. FortiGate unit implements a specific timer before removing an entry in the firewall session table. TCP provides the ability for one end of a connection to terminate its output while still receiving data from the other end. This is called a half-close. FortiGate unit implements a specific timer before removing an entry in the firewall session table.
Question 8
Which two protocols are used to enable administrator access of a FortiGate device? (Choose two.)
- SSH
- HTTPS
- FTM
- FortiTelemetry
Correct answer: AB
Explanation:
Security Guide P29 Reference: https://docs.fortinet.com/document/fortigate/6.4.0/hardening-your-fortigate/99buildingsecurity-into-fortios Security Guide P29
Reference:
https://docs.fortinet.com/document/fortigate/6.4.0/hardening-your-fortigate/99buildingsecurity-into-fortios
Question 9
How does FortiGate act when using SSL VPN in web mode?
- FortiGate acts as an FDS server.
- FortiGate acts as an HTTP reverse proxy.
- FortiGate acts as DNS server.
- FortiGate acts as router.
Correct answer: B
Explanation:
Infrastructure Guide P196 Reference: https://pub.kb.fortinet.com/ksmcontent/Fortinet-Public/current/Fortigate_v4.0MR3/fortigatesslvpn-40-mr3.pdf Infrastructure Guide P196
Reference:
https://pub.kb.fortinet.com/ksmcontent/Fortinet-Public/current/Fortigate_v4.0MR3/fortigatesslvpn-40-mr3.pdf
Question 10
Which three statements explain a flow-based antivirus profile? (Choose three.)
- IPS engine handles the process as a standalone.
- FortiGate buffers the whole file but transmits it to the client simultaneously.
- If the virus is detected, the last packet is delivered to the client.
- Optimized performance compared to proxy-based inspection.
- Flow-based inspection uses a hybrid of scanning modes available in proxy-based inspection.
Correct answer: BDE
Explanation:
Security Guide P350, P351 Reference: https://forum.fortinet.com/tm.aspx?m=192309 Security Guide P350, P351
Reference:
https://forum.fortinet.com/tm.aspx?m=192309
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



