Download Certified Ethical Hacker v10 Exam.312-50v10.TestKing.2019-04-20.142q.vcex
| Vendor: | ECCouncil |
| Exam Code: | 312-50v10 |
| Exam Name: | Certified Ethical Hacker v10 Exam |
| Date: | Apr 20, 2019 |
| File Size: | 298 KB |
| Downloads: | 1 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
A hacker is an intelligent individual with excellent computer skills and the ability to explore a computer’s software and hardware without the owner’s permission.
Their intention can either be to simply gain knowledge or to illegally make changes.
Which of the following class of hacker refers to an individual who works both offensively and defensively at various times?
- White Hat
- Suicide Hacker
- Gray Hat
- Black Hat
Correct answer: C
Question 2
Websites and web portals that provide web services commonly use the Simple Object Access Protocol (SOAP).
Which of the following is an incorrect definition or characteristics of the protocol?
- Based on XML
- Only compatible with the application protocol HTTP
- Exchanges data between web services
- Provides a structured model for messaging
Correct answer: B
Explanation:
Question 3
You have gained physical access to a Windows 2008 R2 server which has an accessible disc drive. When you attempt to boot the server and log in, you are unable to guess the password. In your toolkit, you have an Ubuntu 9.10 Linux LiveCD. Which Linux-based tool can change any user’s password or activate disabled Windows accounts?
- John the Ripper
- SET
- CHNTPW
- Cain & Abel
Correct answer: C
Question 4
What type of vulnerability/attack is it when the malicious person forces the user’s browser to send an authenticated request to a server?
- Cross-site request forgery
- Cross-site scripting
- Session hijacking
- Server side request forgery
Correct answer: A
Question 5
From the following table, identify the wrong answer in terms of Range (ft).
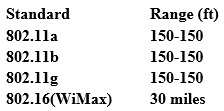
- 802.11b
- 802.11g
- 802.16(WiMax)
- 802.11a
Correct answer: D
Question 6
Steve, a scientist who works in a governmental security agency, developed a technological solution to identify people based on walking patterns and implemented this approach to a physical control access.
A camera captures people walking and identifies the individuals using Steve’s approach.
After that, people must approximate their RFID badges. Both the identifications are required to open the door.
In this case, we can say:
- Although the approach has two phases, it actually implements just one authentication factor
- The solution implements the two authentication factors: physical object and physical characteristic
- The solution will have a high level of false positives
- Biological motion cannot be used to identify people
Correct answer: B
Explanation:
Question 7
Which Intrusion Detection System is the best applicable for large environments where critical assets on the network need extra security and is ideal for observing sensitive network segments?
- Honeypots
- Firewalls
- Network-based intrusion detection system (NIDS)
- Host-based intrusion detection system (HIDS)
Correct answer: C
Question 8
Which of the following is a serious vulnerability in the popular OpenSSL cryptographic software library? This weakness allows stealing the information protected, under normal conditions, by the SSL/TLS encryption used to secure the Internet.
- SSL/TLS Renegotiation Vulnerability
- Shellshock
- Heartbleed Bug
- POODLE
Correct answer: C
Question 9
Which protocol is used for setting up secure channels between two devices, typically in VPNs?
- PPP
- IPSEC
- PEM
- SET
Correct answer: B
Question 10
Which of the following Secure Hashing Algorithm (SHA) produces a 160-bit digest from a message with a maximum length of (264-1) bits and resembles the MD5 algorithm?
- SHA-2
- SHA-3
- SHA-1
- SHA-0
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



