Download Certified Ethical Hacker v10 Exam.312-50v10.Prep4Sure.2018-10-16.85q.vcex
| Vendor: | ECCouncil |
| Exam Code: | 312-50v10 |
| Exam Name: | Certified Ethical Hacker v10 Exam |
| Date: | Oct 16, 2018 |
| File Size: | 288 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Websites and web portals that provide web services commonly use the Simple Object Access Protocol (SOAP). Which of the following is an incorrect definition or characteristics of the protocol?
- Based on XML
- Only compatible with the application protocol HTTP
- Exchanges data between web services
- Provides a structured model for messaging
Correct answer: B
Question 2
You have gained physical access to a Windows 2008 R2 server which has an accessible disc drive. When you attempt to boot the server and log in, you are unable to guess the password. In your toolkit, you have an Ubuntu 9.10 Linux LiveCD. Which Linux-based tool can change any user’s password or activate disabled Windows accounts?
- John the Ripper
- SET
- CHNTPW
- Cain & Abel
Correct answer: C
Explanation:
Question 3
What type of vulnerability/attack is it when the malicious person forces the user’s browser to send an authenticated request to a server?
- Cross-site request forgery
- Cross-site scripting
- Session hijacking
- Server side request forgery
Correct answer: A
Question 4
From the following table, identify the wrong answer in terms of Range (ft).
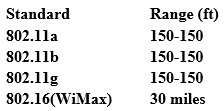
- 802.11b
- 802.11g
- 802.16(WiMax)
- 802.11a
Correct answer: D
Explanation:
Question 5
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is unreachable, ICMP may be disabled and the network may be using TCP. Which tool could the tester use to get a response from a host using TCP?
- Traceroute
- Hping
- TCP ping
- Broadcast ping
Correct answer: B
Question 6
Which of the following types of jailbreaking allows user-level access but does not allow iboot-level access?
- Bootrom Exploit
- iBoot Exploit
- Sandbox Exploit
- Userland Exploit
Correct answer: D
Question 7
What is not a PCI compliance recommendation?
- Use a firewall between the public network and the payment card data.
- Use encryption to protect all transmission of card holder data over any public network.
- Rotate employees handling credit card transactions on a yearly basis to different departments.
- Limit access to card holder data to as few individuals as possible.
Correct answer: C
Question 8
The "white box testing" methodology enforces what kind of restriction?
- Only the internal operation of a system is known to the tester.
- The internal operation of a system is completely known to the tester.
- The internal operation of a system is only partly accessible to the tester.
- Only the external operation of a system is accessible to the tester.
Correct answer: B
Question 9
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.
- SQL injection attack
- Cross-Site Scripting (XSS)
- LDAP Injection attack
- Cross-Site Request Forgery (CSRF)
Correct answer: B
Explanation:
Question 10
The following is part of a log file taken from the machine on the network with the IP address of 192.168.0.110:
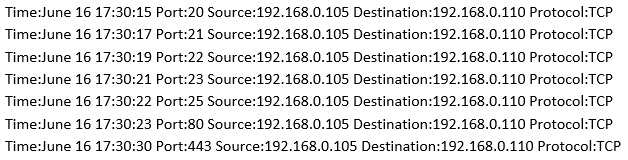
What type of activity has been logged?
- Teardrop attack targeting 192.168.0.110
- Denial of service attack targeting 192.168.0.105
- Port scan targeting 192.168.0.110
- Port scan targeting 192.168.0.105
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



