Download Certified Ethical Hacker v10 Exam.312-50v10.ExamLabs.1999-11-30.182q.vcex
| Vendor: | ECCouncil |
| Exam Code: | 312-50v10 |
| Exam Name: | Certified Ethical Hacker v10 Exam |
| Date: | Nov 30, 1999 |
| File Size: | 750 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed?
- Reverse Social Engineering
- Tailgating
- Piggybacking
- Announced
Correct answer: B
Question 2
An attacker has installed a RAT on a host. The attacker wants to ensure that when a user attempts to go to "www.MyPersonalBank.com", that the user is directed to a phishing site.
Which file does the attacker need to modify?
- Boot.ini
- Sudoers
- Networks
- Hosts
Correct answer: D
Question 3
You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line.
Which command would you use?
- c:\gpedit
- c:\compmgmt.msc
- c:\ncpa.cp
- c:\services.msc
Correct answer: B
Question 4
In Wireshark, the packet bytes panes show the data of the current packet in which format?
- Decimal
- ASCII only
- Binary
- Hexadecimal
Correct answer: D
Question 5
You have successfully gained access to a Linux server and would like to ensure that the succeeding outgoing traffic from this server will not be caught by Network-Based Intrusion Detection Systems (NIDS).
What is the best way to evade the NIDS?
- Out of band signaling
- Protocol Isolation
- Encryption
- Alternate Data Streams
Correct answer: C
Question 6
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.0.0.3. He also needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router, nobody can access to the ftp, and the permitted hosts cannot access the Internet. According to the next configuration, what is happening in the network?
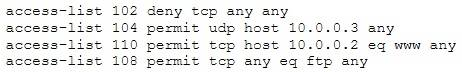
- The ACL 104 needs to be first because is UDP
- The ACL 110 needs to be changed to port 80
- The ACL for FTP must be before the ACL 110
- The first ACL is denying all TCP traffic and the other ACLs are being ignored by the router
Correct answer: D
Question 7
When conducting a penetration test, it is crucial to use all means to get all available information about the target network. One of the ways to do that is by sniffing the network. Which of the following cannot be performed by the passive network sniffing?
- Identifying operating systems, services, protocols and devices
- Modifying and replaying captured network traffic
- Collecting unencrypted information about usernames and passwords
- Capturing a network traffic for further analysis
Correct answer: B
Question 8
Insecure direct object reference is a type of vulnerability where the application does not verify if the user is authorized to access the internal object via its name or key.
Suppose a malicious user Rob tries to get access to the account of a benign user Ned.
Which of the following requests best illustrates an attempt to exploit an insecure direct object reference vulnerability?
- “GET/restricted/goldtransfer?to=Rob&from=1 or 1=1’ HTTP/1.1Host: westbank.com”
- “GET/restricted/accounts/?name=Ned HTTP/1.1 Host: westbank.com”
- “GET/restricted/bank.getaccount(‘Ned’) HTTP/1.1 Host: westbank.com”
- “GET/restricted/\r\n\%00account%00Ned%00access HTTP/1.1 Host: westbank.com”
Correct answer: B
Question 9
Which of these is capable of searching for and locating rogue access points?
- HIDS
- NIDS
- WISS
- WIPS
Correct answer: D
Question 10
A hacker is an intelligent individual with excellent computer skills and the ability to explore a computer’s software and hardware without the owner’s permission. Their intention can either be to simply gain knowledge or to illegally make changes.
Which of the following class of hacker refers to an individual who works both offensively and defensively at various times?
- White Hat
- Suicide Hacker
- Gray Hat
- Black Hat
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



