Download Certified Ethical Hacker v10 Exam.312-50v10.ActualTests.2019-01-28.176q.vcex
| Vendor: | ECCouncil |
| Exam Code: | 312-50v10 |
| Exam Name: | Certified Ethical Hacker v10 Exam |
| Date: | Jan 28, 2019 |
| File Size: | 509 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
The "white box testing" methodology enforces what kind of restriction?
- Only the internal operation of a system is known to the tester.
- The internal operation of a system is completely known to the tester.
- The internal operation of a system is only partly accessible to the tester.
- Only the external operation of a system is accessible to the tester.
Correct answer: B
Question 2
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.
- SQL injection attack
- Cross-Site Scripting (XSS)
- LDAP Injection attack
- Cross-Site Request Forgery (CSRF)
Correct answer: B
Question 3
This tool is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, as well as the PTW attack, thus making the attack much faster compared to other WEP cracking tools.
Which of the following tools is being described?
- wificracker
- Airguard
- WLAN-crack
- Aircrack-ng
Correct answer: D
Question 4
The following is part of a log file taken from the machine on the network with the IP address of 192.168.0.110:
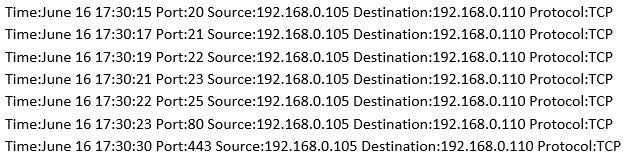
What type of activity has been logged?
- Teardrop attack targeting 192.168.0.110
- Denial of service attack targeting 192.168.0.105
- Port scan targeting 192.168.0.110
- Port scan targeting 192.168.0.105
Correct answer: C
Question 5
You are attempting to run an Nmap port scan on a web server.
Which of the following commands would result in a scan of common ports with the least amount of noise in order to evade IDS?
- nmap –A - Pn
- nmap –sP –p-65535-T5
- nmap –sT –O –T0
- nmap –A --host-timeout 99-T1
Correct answer: C
Question 6
Bob, your senior colleague, has sent you a mail regarding aa deal with one of the clients. You are requested to accept the offer and you oblige.
After 2 days, Bob denies that he had ever sent a mail.
What do you want to “know” to prove yourself that it was Bob who had send a mail?
- Confidentiality
- Integrity
- Non-Repudiation
- Authentication
Correct answer: C
Question 7
What is attempting an injection attack on a web server based on responses to True/False questions called?
- DMS-specific SQLi
- Compound SQLi
- Blind SQLi
- Classic SQLi
Correct answer: C
Question 8
The establishment of a TCP connection involves a negotiation called three-way handshake. What type of message does the client send to the server in order to begin this negotiation?
- ACK
- SYN
- RST
- SYN-ACK
Correct answer: B
Question 9
You need a tool that can do network intrusion prevention and intrusion detection, function as a network sniffer, and record network activity. What tool would you most likely select?
- Snort
- Nmap
- Cain & Abel
- Nessus
Correct answer: A
Question 10
Which of the following will perform an Xmas scan using NMAP?
- nmap -sA 192.168.1.254
- nmap -sP 192.168.1.254
- nmap -sX 192.168.1.254
- nmap -sV 192.168.1.254
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



