Download Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR).350-401.ITExamAnswers.2021-11-03.265q.vcex
| Vendor: | Cisco |
| Exam Code: | 350-401 |
| Exam Name: | Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR) |
| Date: | Nov 03, 2021 |
| File Size: | 23 MB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
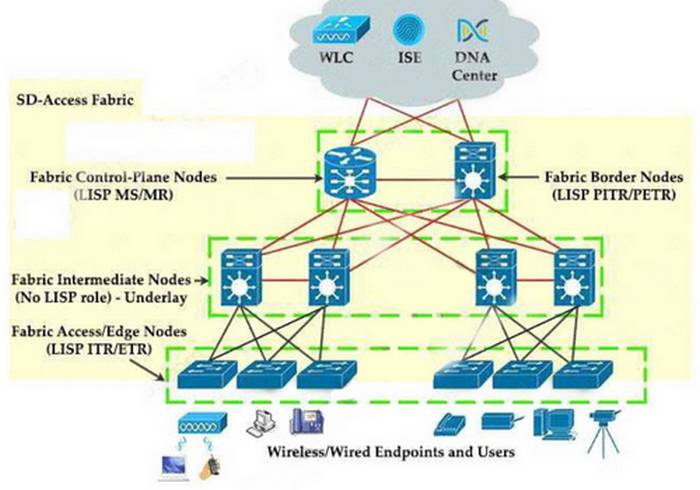
Which function does a fabric edge node perform in an SD-Access deployment?
- Connects endpoints to the fabric and forwards their traffic.
- Encapsulates end-user data traffic into LISP.
- Connects the SD-Access fabric to another fabric or external Layer 3 networks.
- Provides reachability between border nodes in the fabric underlay.
Correct answer: A
Explanation:
There are five basic device roles in the fabric overlay:Control plane node: This node contains the settings, protocols, and mapping tables to provide the endpoint-to-location (EID-to-RLOC) mapping system for the fabric overlay.Fabric border node: This fabric device (for example, core layer device) connects external Layer 3 networks to the SDA fabric.Fabric edge node: This fabric device (for example, access or distribution layer device) connects wired endpoints to the SDA fabric.Fabric WLAN controller (WLC): This fabric device connects APs and wireless endpoints to the SDA fabric.Intermediate nodes: These are intermediate routers or extended switches that do not provide any sort of SD-Access fabric role other than underlay services. There are five basic device roles in the fabric overlay:
- Control plane node: This node contains the settings, protocols, and mapping tables to provide the endpoint-to-location (EID-to-RLOC) mapping system for the fabric overlay.
- Fabric border node: This fabric device (for example, core layer device) connects external Layer 3 networks to the SDA fabric.
- Fabric edge node: This fabric device (for example, access or distribution layer device) connects wired endpoints to the SDA fabric.
- Fabric WLAN controller (WLC): This fabric device connects APs and wireless endpoints to the SDA fabric.
- Intermediate nodes: These are intermediate routers or extended switches that do not provide any sort of SD-Access fabric role other than underlay services.
Question 2
Refer to the exhibit.Which privilege level is assigned to VTY users?
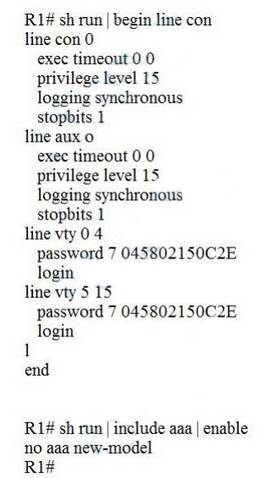
- 1
- 7
- 13
- 15
Correct answer: A
Explanation:
Lines (CON, AUX, VTY) default to level 1 privileges. Lines (CON, AUX, VTY) default to level 1 privileges.
Question 3
Which requirement for an Ansible-managed node is true?
- It must have an SSH server running.
- It must be a Linux server or a Cisco device.
- It must support ad hoc commands.
- It must have an Ansible Tower installed.
Correct answer: A
Question 4
Which OSPF network types are compatible and allow communication through the two peering devices?
- point-to-multipoint to nonbroadcast
- broadcast to nonbroadcast
- point-to-multipoint to broadcast
- broadcast to point-to-point
Correct answer: B
Explanation:
The following different OSPF types are compatible with each other:Broadcast and Non-Broadcast (adjust hello/dead timers) Point-to-Point and Point-to-Multipoint (adjust hello/dead timers) Broadcast and Non-Broadcast networks elect DR/BDR so they are compatible. Point-topoint/ multipoint do not elect DR/BDR so they are compatible. Reference: Click here The following different OSPF types are compatible with each other:
- Broadcast and Non-Broadcast (adjust hello/dead timers)
- Point-to-Point and Point-to-Multipoint (adjust hello/dead timers)
Broadcast and Non-Broadcast networks elect DR/BDR so they are compatible. Point-topoint/ multipoint do not elect DR/BDR so they are compatible.
Reference: Click here
Question 5
Which NGFW mode blocks flows crossing the firewall?
- tap
- inline
- passive
- inline tap
Correct answer: B
Explanation:
Firepower Threat Defense (FTD) provides six interface modes which are: Routed, Switched, Inline Pair, Inline Pair with Tap, Passive, Passive (ERSPAN).When Inline Pair Mode is in use, packets can be blocked since they are processed inline When you use Inline Pair mode, the packet goes mainly through the FTD Snort engine When Tap Mode is enabled, a copy of the packet is inspected and dropped internally while the actual traffic goes through FTD unmodified Reference: Click here Firepower Threat Defense (FTD) provides six interface modes which are: Routed, Switched, Inline Pair, Inline Pair with Tap, Passive, Passive (ERSPAN).
When Inline Pair Mode is in use, packets can be blocked since they are processed inline When you use Inline Pair mode, the packet goes mainly through the FTD Snort engine When Tap Mode is enabled, a copy of the packet is inspected and dropped internally while the actual traffic goes through FTD unmodified
Reference: Click here
Question 6
Which statement about route targets is true when using VRF-Lite?
- Route targets control the import and export of routes into a customer routing table.
- When BGP is configured, route targets are transmitted as BGP standard communities.
- Route targets allow customers to be assigned overlapping addresses.
- Route targets uniquely identify the customer routing table.
Correct answer: A
Explanation:
Answer ‘Route targets allow customers to be assigned overlapping addresses’ and answer ‘Route targets uniquely identify the customer routing table’ are not correct as only route distinguisher (RD) identifies the customer routing table and “allows customers to be assigned overlapping addresses”. Answer ‘When BGP is configured, route targets are transmitted as BGP standard communities’ is not correct as “When BGP is configured, route targets are transmitted as BGP extended communities” Answer ‘Route targets allow customers to be assigned overlapping addresses’ and answer ‘Route targets uniquely identify the customer routing table’ are not correct as only route distinguisher (RD) identifies the customer routing table and “allows customers to be assigned overlapping addresses”.
Answer ‘When BGP is configured, route targets are transmitted as BGP standard communities’ is not correct as “When BGP is configured, route targets are transmitted as BGP extended communities”
Question 7
Refer to the exhibit. Which statement about the OPSF debug output is true?
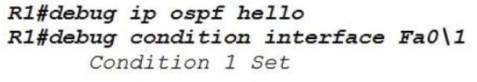
- The output displays OSPF hello messages which router R1 has sent or received on interface Fa0/1.
- The output displays OSPF messages which router R1 has sent or received on all interfaces.
- The output displays OSPF messages which router R1 has sent or received on interface Fa0/1.
- The output displays OSPF hello and LSACK messages which router R1 has sent or received.
Correct answer: A
Explanation:
This combination of commands is known as “Conditional debug” and will filter the debug output based on your conditions. Each condition added, will behave like an ‘And’ operator in Boolean logic. Some examples of the “debug ip ospf hello” are shown below: This combination of commands is known as “Conditional debug” and will filter the debug output based on your conditions. Each condition added, will behave like an ‘And’ operator in Boolean logic.
Some examples of the “debug ip ospf hello” are shown below:

Question 8
Which feature does Cisco TrustSec use to provide scalable, secure communication throughout a network?
- security group tag ACL assigned to each port on a switch
- security group tag number assigned to each user on a switch
- security group tag number assigned to each port on a network
- security group tag ACL assigned to each router on a network
Correct answer: B
Explanation:
https://www.cisco.com/c/dam/en/us/solutions/collateral/borderless-networks/trustsec/C07-730151-00_overview_of_trustSec_og.pdf https://www.cisco.com/c/dam/en/us/solutions/collateral/borderless-networks/trustsec/C07-730151-00_overview_of_trustSec_og.pdf
Question 9
An engineer configures a WLAN with fast transition enabled. Some legacy clients fail to connect to this WLAN.
Which feature allows the legacy clients to connect while still allowing other clients to use fast transition based on their OUIs?
- over the DS
- 802.11k
- adaptive R
- 802.11v
Correct answer: C
Explanation:
802.11r Fast Transition (FT) Roaming is an amendment to the 802.11 IEEE standards. It is a new concept for roaming. The initial handshake with the new AP occurs before client roams to the target AP. Therefor it is called Fast Transition. 802.11rprovides two methods of roaming:Over-the-air: With this type of roaming, the client communicates directly with the target AP using IEEE 802.11authentication with the Fast Transition (FT) authentication algorithm.Over-the-DS (distribution system): With this type of roaming, the client communicates with the target AP through the current AP. The communication between the client and the target AP is carried in FT action frames between the client and the current AP and is then sent through the controller.But both of these methods do not deal with legacy clients. The 802.11k allows 11k capable clients to request a neighbor report containing information about known neighbor APs that are candidates for roaming. Click hereClick here IEEE 802.11v is an amendment to the IEEE 802.11 standard which describes numerous enhancements to wireless network management. One such enhancement is Network assisted Power Savings which helps clients to improve the battery life by enabling them to sleep longer. Another enhancement is Network assisted Roaming which enables the WLAN to send requests to associated clients, advising the clients as to better APs to associate to. This is useful for both load balancing and in directing poorly connected clients. Click hereClick here Cisco 802.11r supports three modes:Pure mode: only allows 802.11r client to connectMixed mode: allows both clients that do and do not support FT to connect Adaptive mode: does not advertise the FT AKM at all, but will use FT when supported clients connect Therefore “Adaptive mode” is the best answer here. 802.11r Fast Transition (FT) Roaming is an amendment to the 802.11 IEEE standards. It is a new concept for roaming. The initial handshake with the new AP occurs before client roams to the target AP. Therefor it is called Fast Transition. 802.11rprovides two methods of roaming:
- Over-the-air: With this type of roaming, the client communicates directly with the target AP using IEEE 802.11authentication with the Fast Transition (FT) authentication algorithm.
- Over-the-DS (distribution system): With this type of roaming, the client communicates with the target AP through the current AP. The communication between the client and the target AP is carried in FT action frames between the client and the current AP and is then sent through the controller.
But both of these methods do not deal with legacy clients.
The 802.11k allows 11k capable clients to request a neighbor report containing information about known neighbor APs that are candidates for roaming.
Click hereClick here
IEEE 802.11v is an amendment to the IEEE 802.11 standard which describes numerous enhancements to wireless network management. One such enhancement is Network assisted Power Savings which helps clients to improve the battery life by enabling them to sleep longer. Another enhancement is Network assisted Roaming which enables the WLAN to send requests to associated clients, advising the clients as to better APs to associate to. This is useful for both load balancing and in directing poorly connected clients.
Click hereClick here
Cisco 802.11r supports three modes:
- Pure mode: only allows 802.11r client to connect
- Mixed mode: allows both clients that do and do not support FT to connect
- Adaptive mode: does not advertise the FT AKM at all, but will use FT when supported clients connect Therefore “Adaptive mode” is the best answer here.
Question 10
Which statements are used for error handling in Python?
- try/catch
- catch/release
- block/rescue
- try/except
Correct answer: D
Explanation:
The words “try” and “except” are Python keywords and are used to catch exceptions. For example:try:print 1/0 except ZeroDivisionError:print ‘Error! We cannot divide by zero!!!’ The words “try” and “except” are Python keywords and are used to catch exceptions. For example:
try:
print 1/0
except ZeroDivisionError:
print ‘Error! We cannot divide by zero!!!’
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



