Download CCNP Security Implementing Cisco Threat Control Solutions.300-210.RealTests.2019-10-22.270q.vcex
| Vendor: | Cisco |
| Exam Code: | 300-210 |
| Exam Name: | CCNP Security Implementing Cisco Threat Control Solutions |
| Date: | Oct 22, 2019 |
| File Size: | 10 MB |
| Downloads: | 1 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
Which three operating systems are supported with Cisco AMP for Endpoints? (Choose three.)
- Windows
- AWS
- Android
- Cisco IOS
- OS X
- ChromeOS
Correct answer: ACE
Question 2
Which Cisco Web Security Appliance feature enables the appliance to block suspicious traffic on all of its ports and IP addresses?
- explicit forward mode
- Layer 4 Traffic Monitor
- transparent mode
- Secure Web Proxy
Correct answer: B
Question 3
Which feature requires the network discovery policy for it to work on the Cisco Next Generation Intrusion Prevention System?
- impact flags
- URL filtering
- security intelligence
- health monitoring
Correct answer: C
Question 4
What are two arguments that can be used with the show content-scan command in Cisco IOS software? (Choose two.)
- data
- session
- buffer
- statistics
- verbose
Correct answer: BD
Question 5
What is a difference between a Cisco Content Security Management virtual appliance and a physical appliance?
- Migration between virtual appliances of varying sizes is possible, but physical appliances must be of equal size.
- The virtual appliance requires an additional license to run on a host.
- The physical appliance requires an additional license to activate its adapters.
- The physical appliance is configured with a DHCP-enabled management port to receive an IP address automatically, but you must assign the virtual appliance an IP address manually in your management subnet.
Correct answer: B
Question 6
Which detection method is also known as machine learning on Network-based Cisco Advanced Malware Protection?
- custom file detection
- hashing
- Spero engine
- dynamic analysis
Correct answer: C
Question 7
Which Cisco Firepower rule action displays a HTTP warning page and resets the connection of HTTP traffic specified in the access control rule?
- Interactive Block with Reset
- Block
- Allow with Warning
- Interactive Block
Correct answer: A
Question 8
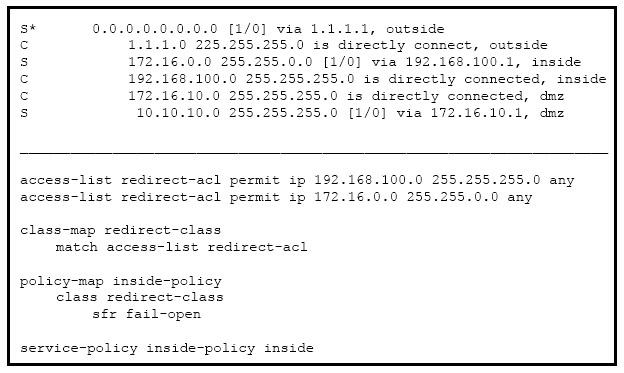
Refer to the exhibit. Which option is a result of this configuration?
- All ingress traffic on the inside interface that matches the access list is redirected.
- All egress traffic on the outside interface that matches the access list if redirected.
- All TCP traffic that arrives on the inside interface is redirected.
- All ingress traffic that arrives on the inside interface is redirected.
- All ingress and egress traffic is redirected to the Cisco FirePOWER module.
Correct answer: E
Question 9
What are two requirements for configuring a hybrid interface in FirePOWER? (Choose two.)
- virtual network
- virtual router
- virtual appliance
- virtual switch
- virtual context
Correct answer: BD
Question 10
When you configure the Cisco ESA to perform blacklisting, what are two items you can disable to enhance performance? (Choose two.)
- rootkit detection
- spam scanning
- APT detection
- antivirus scanning
- URL filtering
Correct answer: BD
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



