Download Check Point Certified Security Administrator.156-215.80.SelfTestEngine.2019-05-08.275q.vcex
| Vendor: | Checkpoint |
| Exam Code: | 156-215.80 |
| Exam Name: | Check Point Certified Security Administrator |
| Date: | May 08, 2019 |
| File Size: | 6 MB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
An administrator is creating an IPsec site-to-site VPN between his corporate office and branch office. Both offices are protected by Check Point Security Gateway managed by the same Security Management Server. While configuring the VPN community to specify the pre-shared secret the administrator found that the check box to enable pre-shared secret is shared and cannot be enabled. Why does it not allow him to specify the pre-shared secret?
- IPsec VPN blade should be enabled on both Security Gateway.
- Pre-shared can only be used while creating a VPN between a third party vendor and Check Point Security Gateway.
- Certificate based Authentication is the only authentication method available between two Security Gateway managed by the same SMS.
- The Security Gateways are pre-R75.40.
Correct answer: C
Question 2
ABC Corp., and have recently returned from a training course on Check Point's new advanced R80 management platform. You are presenting an in-house R80
Management to the other administrators in ABC Corp.
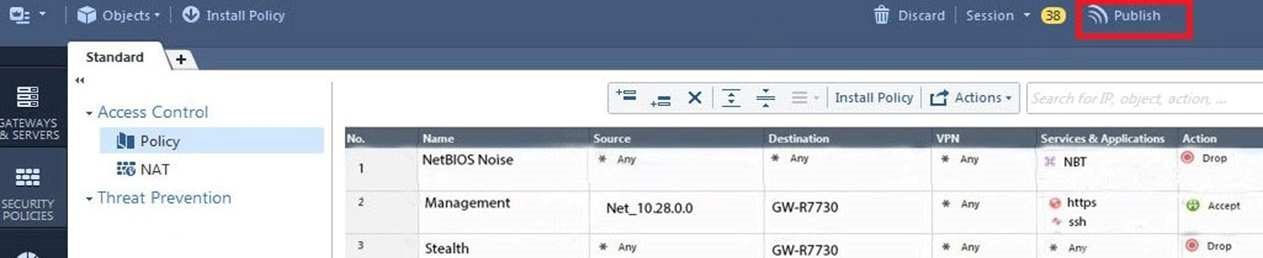
How will you describe the new “Publish” button in R80 Management Console?
- The Publish button takes any changes an administrator has made in their management session, publishes a copy to the Check Point of R80, and then saves it to the R80 database.
- The Publish button takes any changes an administrator has made in their management session and publishes a copy to the Check Point Cloud of R80 and but does not save it to the R80
- The Publish button makes any changes an administrator has made in their management session visible to all other administrator sessions and saves it to the Database.
- The Publish button makes any changes an administrator has made in their management session visible to the new Unified Policy session and saves it to the Database.
Correct answer: C
Explanation:
To make your changes available to other administrators, and to save the database before installing a policy, you must publish the session. When you publish a session, a new database version is created. Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197 To make your changes available to other administrators, and to save the database before installing a policy, you must publish the session. When you publish a session, a new database version is created.
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197
Question 3
Which of the following ClusterXL modes uses a non-unicast MAC address for the cluster IP address.
- High Availability
- Load Sharing Multicast
- Load Sharing Pivot
- Master/Backup
Correct answer: B
Explanation:
ClusterXL uses the Multicast mechanism to associate the virtual cluster IP addresses with all cluster members. By binding these IP addresses to a Multicast MAC address, it ensures that all packets sent to the cluster, acting as a gateway, will reach all members in the cluster. Reference:https://sc1.checkpoint.com/documents/R76/CP_R76_ClusterXL_AdminGuide/7292.htm ClusterXL uses the Multicast mechanism to associate the virtual cluster IP addresses with all cluster members. By binding these IP addresses to a Multicast MAC address, it ensures that all packets sent to the cluster, acting as a gateway, will reach all members in the cluster.
Reference:
https://sc1.checkpoint.com/documents/R76/CP_R76_ClusterXL_AdminGuide/7292.htm
Question 4
Fill in the blank: With the User Directory Software Blade, you can create R80 user definitions on a(an) ___________ Server.
- NT domain
- SMTP
- LDAP
- SecurID
Correct answer: C
Explanation:
Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197 Reference: https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197
Question 5
Which of the following is NOT a component of a Distinguished Name?
- Organization Unit
- Country
- Common name
- User container
Correct answer: D
Explanation:
Distinguished Name Components CN=common name, OU=organizational unit, O=organization, L=locality, ST=state or province, C=country name Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950 Distinguished Name Components
CN=common name, OU=organizational unit, O=organization, L=locality, ST=state or province, C=country name
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950
Question 6
What are the three authentication methods for SIC?
- Passwords, Users, and standards-based SSL for the creation of security channels
- Certificates, standards-based SSL for the creation of secure channels, and 3DES or AES128 for encryption
- Packet Filtering, certificates, and 3DES or AES128 for encryption
- Certificates, Passwords, and Tokens
Correct answer: B
Explanation:
Secure Internal Communication (SIC) Secure Internal Communication (SIC) lets Check Point platforms and products authenticate with each other. The SIC procedure creates a trusted status between gateways, management servers and other Check Point components. SIC is required to install polices on gateways and to send logs between gateways and management servers. These security measures make sure of the safety of SIC:Certificates for authentication Standards-based SSL for the creation of the secure channel 3DES for encryption Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950 Secure Internal Communication (SIC)
Secure Internal Communication (SIC) lets Check Point platforms and products authenticate with each other. The SIC procedure creates a trusted status between gateways, management servers and other Check Point components. SIC is required to install polices on gateways and to send logs between gateways and management servers.
These security measures make sure of the safety of SIC:
- Certificates for authentication
- Standards-based SSL for the creation of the secure channel
- 3DES for encryption
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_SecMan_WebAdmin/html_frameset.htm?topic=documents/R76/CP_R76_SecMan_WebAdmin/71950
Question 7
You have enabled “Full Log” as a tracking option to a security rule. However, you are still not seeing any data type information. What is the MOST likely reason?
- Logging has disk space issues. Change logging storage options on the logging server or Security Management Server properties and install database.
- Data Awareness is not enabled.
- Identity Awareness is not enabled.
- Logs are arriving from Pre-R80 gateways.
Correct answer: A
Explanation:
The most likely reason for the logs data to stop is the low disk space on the logging device, which can be the Management Server or the Gateway Server. The most likely reason for the logs data to stop is the low disk space on the logging device, which can be the Management Server or the Gateway Server.
Question 8
What is the order of NAT priorities?
- Static NAT, IP pool NAT, hide NAT
- IP pool NAT, static NAT, hide NAT
- Static NAT, automatic NAT, hide NAT
- Static NAT, hide NAT, IP pool NAT
Correct answer: A
Explanation:
The order of NAT priorities is:Static NAT IP Pool NAT Hide NAT Since Static NAT has all of the advantages of IP Pool NAT and more, it has a higher priority than the other NAT methods. Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm#o6919 The order of NAT priorities is:
- Static NAT
- IP Pool NAT
- Hide NAT
Since Static NAT has all of the advantages of IP Pool NAT and more, it has a higher priority than the other NAT methods.
Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_Firewall_WebAdmin/6724.htm#o6919
Question 9
Which of the following is an identity acquisition method that allows a Security Gateway to identify Active Directory users and computers?
- UserCheck
- Active Directory Query
- Account Unit Query
- User Directory Query
Correct answer: B
Explanation:
AD Query extracts user and computer identity information from the Active Directory Security Event Logs. The system generates a Security Event log entry when a user or computer accesses a network resource. For example, this occurs when a user logs in, unlocks a screen, or accesses a network drive. Reference : https://sc1.checkpoint.com/documents/R76/CP_R76_IdentityAwareness_AdminGuide/62402.htm AD Query extracts user and computer identity information from the Active Directory Security Event Logs. The system generates a Security Event log entry when a user or computer accesses a network resource. For example, this occurs when a user logs in, unlocks a screen, or accesses a network drive.
Reference : https://sc1.checkpoint.com/documents/R76/CP_R76_IdentityAwareness_AdminGuide/62402.htm
Question 10
Ken wants to obtain a configuration lock from other administrator on R80 Security Management Server. He can do this via WebUI or a via CLI. Which command should be use in CLI? Choose the correct answer.
- remove database lock
- The database feature has one command lock database override.
- override database lock
- The database feature has two commands: lock database override and unlock database. Both will work.
Correct answer: D
Explanation:
Use the database feature to obtain the configuration lock. The database feature has two commands: lock database [override]. unlock database The commands do the same thing: obtain the configuration lock from another administrator. Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Gaia_WebAdmin/75697.htm#o73091 Use the database feature to obtain the configuration lock. The database feature has two commands:
- lock database [override].
- unlock database
The commands do the same thing: obtain the configuration lock from another administrator.
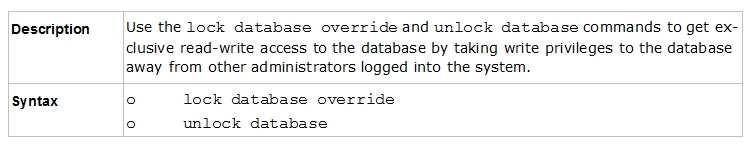
Reference: https://sc1.checkpoint.com/documents/R76/CP_R76_Gaia_WebAdmin/75697.htm#o73091
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



