Download BTA Certified Blockchain Solution Architect.CBSA.TestKing.2019-07-06.98q.vcex
| Vendor: | Blockchain |
| Exam Code: | CBSA |
| Exam Name: | BTA Certified Blockchain Solution Architect |
| Date: | Jul 06, 2019 |
| File Size: | 354 KB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
What is a logic gate in electronics and computer science?
- A logic gate usually takes in 2 inputs and gives out 1 output. The inputs and outputs are binary values, meaning they can be both 1 and 0.
- A logic gate usually takes in 3 inputs and gives out 2 output. The inputs and outputs are binary values, meaning they can be 1 or 0.
- A logic gate usually takes in 2 inputs and gives out 6 output. The inputs and outputs are binary values, meaning they can be both 1 and 0.
- A logic gate usually takes in 2 inputs and gives out 1 output. The inputs and outputs are binary values, meaning they can be 1 or 0.
Correct answer: D
Explanation:
A logic gate usually takes in 2 inputs and gives out 1 output. The inputs and outputs are binary values, meaning they can be 1 or 0. A XOR logic gate takes in 2 binary inputs and gives out a high output ONLY when the inputs are different. Meaning, if A and B are inputted to a XOR gate then the out C will be 1 ONLY when A is not equal to B. Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/ A logic gate usually takes in 2 inputs and gives out 1 output. The inputs and outputs are binary values, meaning they can be 1 or 0. A XOR logic gate takes in 2
binary inputs and gives out a high output ONLY when the inputs are different. Meaning, if A and B are inputted to a XOR gate then the out C will be 1 ONLY when A
is not equal to B.
Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/
Question 2
Ethereum is considered to be a ______________type of blockchain.
- Permissionless
- Permission Based
- Hybrid
- Private
Correct answer: A
Explanation:
Permissionless - anyone can join Anyone can run a node, run mining software/hardware, access a wallet and write data onto and transact within the blockchain (as long as they follow the rules of the bitcoin blockchain). There is no way to censor anyone, ever, on the permissionless bitcoin blockchain. Reference: https://medium.com/@dustindreifuerst/permissioned-vs-permissionless-blockchains-acb8661ee095 Permissionless - anyone can join Anyone can run a node, run mining software/hardware, access a wallet and write data onto and transact within the blockchain (as long as they follow the rules of the bitcoin blockchain). There is no way to censor anyone, ever, on the permissionless bitcoin blockchain.
Reference: https://medium.com/@dustindreifuerst/permissioned-vs-permissionless-blockchains-acb8661ee095
Question 3
Your company working for is now considering the blockchain. They would like to perform a POC with R3 Corda. The CIO was reading about different blockchain consensus algos and would like to understand what type of consensus algos is used with Corda.
What is the best answer?
- R3 Corda is a pluggable blockchain and allows the enterprise flexibility
- R3 Corda is a byzantine fault tolerant blokchain
- R3 Corda is a proof of stake based blockchain
- R3 Corda is a proof of work based blockchain
Correct answer: A
Explanation:
Corda does not share the same requirements as Bitcoin: we require absolute certainty over transaction finality and we need to know who our counterparts are. So we had the freedom – and took this opportunity – to solve the consensus problem in a different way. In particular, Corda solves the privacy issue in a number of manners, primarily by allowing for separation of consensus into a service which we call the Notary Cluster. Corda was designed for business from the start. It has no cryptocurrency built into the platform and does not require mining-style consensus, which imposes great cost with little business benefit. Corda does not share the same requirements as Bitcoin: we require absolute certainty over transaction finality and we need to know who our counterparts are. So we had the freedom – and took this opportunity – to solve the consensus problem in a different way. In particular, Corda solves the privacy issue in a number of manners, primarily by allowing for separation of consensus into a service which we call the Notary Cluster. Corda was designed for business from the start. It has no cryptocurrency built into the platform and does not require mining-style consensus, which imposes great cost with little business benefit.
Question 4
Secure Hash Algorithm (SHA-256) output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes). Select best answer.
- NSA is spying on us so what’s it matters.
- Depends on input
- False
- True
Correct answer: D
Explanation:
SHA stands for Secure Hash Algorithm. This is used to prove data integrity. The same input(s) will always produce the exact same output. This output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes). Reference: https://medium.com/all-things-ledger/bitcoins-implementation-of-blockchain-2be713f662c2 SHA stands for Secure Hash Algorithm. This is used to prove data integrity. The same input(s) will always produce the exact same output. This output is always 256 bits or 32 bytes in length regardless of the length of the input (even if input is millions of bytes).
Reference: https://medium.com/all-things-ledger/bitcoins-implementation-of-blockchain-2be713f662c2
Question 5
In the Ethereum EVM there are two types of memory areas. (Select two.)
- Storage
- Database
- Memory
- Persistent
- Ephemeral
Correct answer: AC
Explanation:
Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine Reference: https://solidity.readthedocs.io/en/latest/introduction-to-smart-contracts.html#the-ethereum-virtual-machine
Question 6
What are some advantages of Proof of Stake(POS) mining over Proof of Work(POW) mining? (Select three.)
- Energy efficient in regards to that it could consume for electricity as compared to PoW
- Faster Hashing algorithms
- No need for expensive compared to POW
- Faster validations compared to POW
- Better blockchain security compared to POW
Correct answer: ACD
Explanation:
This eliminates the below challenges from PoW and believed to have an advantage. No need of expensive hardware (a normal laptop or computer running the respective coin’s Validator client will do as long as your laptop or computer is online) Energy efficient as it won’t consume high electricity as PoW does More loyal Validators As higher the stake the Validators have for a long time, more chances for the Validator to be picked up for “forging” and earn the transaction fee Faster validations Reference: https://medium.com/@karthik.seshu/cryptocurrency-proof-of-work-vs-proof-of-stake-e1eee1420b10 This eliminates the below challenges from PoW and believed to have an advantage.
No need of expensive hardware (a normal laptop or computer running the respective coin’s Validator client will do as long as your laptop or computer is online) Energy efficient as it won’t consume high electricity as PoW does More loyal Validators As higher the stake the Validators have for a long time, more chances for the Validator to be picked up for “forging” and earn the transaction fee Faster validations
Reference: https://medium.com/@karthik.seshu/cryptocurrency-proof-of-work-vs-proof-of-stake-e1eee1420b10
Question 7
Application Specific Integrated Circuit (ASIC) are used always in enterprise blockchains.
- TRUE
- FALSE
Correct answer: B
Explanation:
ASICS are generally used in blockchains such as BTC that have a Proof of Work consensus due to competition Reference: https://www.trymining.com/pages/asic-vs-gpu ASICS are generally used in blockchains such as BTC that have a Proof of Work consensus due to competition
Reference: https://www.trymining.com/pages/asic-vs-gpu
Question 8
What type of encryption is shown below and is commonly used in blockchain cryptography?
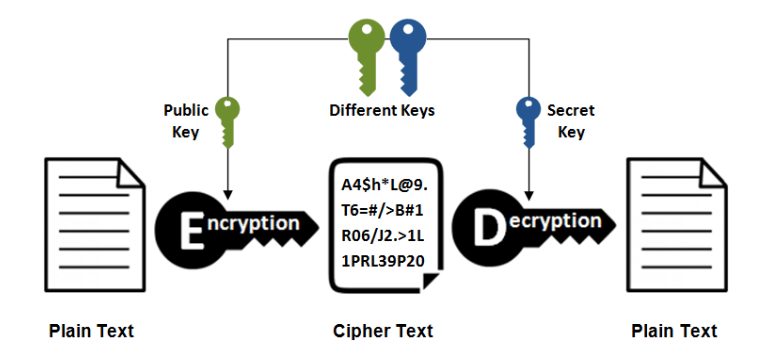
- Diffie-Hellman
- Asymmetric Encryption
- Synchronous
- Asynchronous
- Symmetric Encryption
Correct answer: B
Explanation:
Asymmetric cryptography utilizes two different keys, a public key and a private to encrypt and decrypt a particular data. The use of one key cancels out the use of the other. Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/ Asymmetric cryptography utilizes two different keys, a public key and a private to encrypt and decrypt a particular data. The use of one key cancels out the use of the other.
Reference: https://blockgeeks.com/guides/cryptocurrencies-cryptography/
Question 9
Contracts live on the blockchain in an Ethereum-specific binary format called _____________?
- EOS
- EVM Code
- Ether
- Gas
- EVM Bytecode
Correct answer: E
Explanation:
The Ethereum Virtual Machine (EVM) is the runtime environment for smart contracts in Ethereum. It is not only sandboxed, but actually completely isolated, which means that code running inside the EVM has no access to network, filesystem, or other processes. Smart contracts even have limited access to other smart contracts. Reference: http://ethdocs.org/en/latest/contracts-and-transactions/developer-tools.html#the-evm The Ethereum Virtual Machine (EVM) is the runtime environment for smart contracts in Ethereum. It is not only sandboxed, but actually completely isolated, which means that code running inside the EVM has no access to network, filesystem, or other processes. Smart contracts even have limited access to other smart contracts.
Reference: http://ethdocs.org/en/latest/contracts-and-transactions/developer-tools.html#the-evm
Question 10
Bitcoin uses what proof of work consensus system?
- Cubehash512
- Scrypt-Jane
- Whirlpool
- Scrypt-n
- Hashcash
Correct answer: E
Explanation:
Bitcoin uses the Hashcash proof of work system. Reference: https://en.bitcoin.it/wiki/Hashcash Bitcoin uses the Hashcash proof of work system.
Reference: https://en.bitcoin.it/wiki/Hashcash
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



